Introduction
A packet sniffer is a tool that can capture and analyze packets that are going to, leaving or going through the router. Packet sniffing is very useful when you diagnose networks or protect against security attacks over networks.
Packet Sniffer configuration
RouterOS embedded sniffer allows you to capture packets based on various protocols.
In the following example, we will configure sniffer to match packets going through the ether1 interface:
[admin@MikroTik] > /tool/sniffer/start interface=ether1 [admin@MikroTik] > /tool/sniffer/stop [admin@MikroTik] > /tool/sniffer/save file-name=/flash/test.pcap MikroTik] > file print where name~"test" Columns: NAME, TYPE, SIZE, CREATION-TIME # NAME TYPE SIZE CREATION-TIME 9 flash/test.pcap file 3696 dec/04/2019 10:48:16
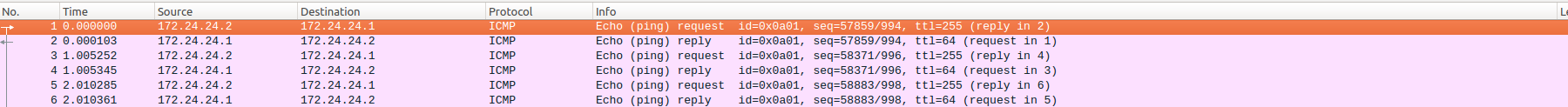
You can download captured packets from a file section. Then you can use packet analyzer such as Wireshark to analyze a file:
Packet Sniffer Quick Mode
The quick mode will display results as they are filtered out with a limited size buffer for packets. There are several attributes that can be set up filtering. If no attributes are set current configuration will be used.
[admin@MikroTik] > /tool/sniffer/quick ip-protocol=icmp Columns: INTERFace, TIME, NUm, DIr, SRC-MAC, DST-MAC, SRC-ADDRESS, DST-ADDRESS, PROTOCOl, SIze, Cpu, FP INTERF TIME NU DI SRC-MAC DST-MAC SRC-ADDRESS DST-ADDRESS PROTOCO SI C FP ether7 35.472 79 <- 6C:3B:6B:ED:83:69 6C:3B:6B:ED:81:83 10.155.126.252 10.155.126.253 ip:icmp 70 7 no ether7 35.472 80 -> 6C:3B:6B:ED:81:83 6C:3B:6B:ED:83:69 10.155.126.253 10.155.126.252 ip:icmp 70 7 no ether1 35.595 81 <- 6C:3B:6B:ED:83:63 6C:3B:6B:ED:81:7D 172.24.24.2 172.24.24.1 ip:icmp 70 4 no ether1 35.595 82 -> 6C:3B:6B:ED:81:7D 6C:3B:6B:ED:83:63 172.24.24.1 172.24.24.2 ip:icmp 70 4 no ether7 36.457 83 <- 6C:3B:6B:ED:83:69 6C:3B:6B:ED:81:83 10.155.126.252 10.155.126.253 ip:icmp 70 7 no ether7 36.457 84 -> 6C:3B:6B:ED:81:83 6C:3B:6B:ED:83:69 10.155.126.253 10.155.126.252 ip:icmp 70 7 no ether1 36.6 85 <- 6C:3B:6B:ED:83:63 6C:3B:6B:ED:81:7D 172.24.24.2 172.24.24.1 ip:icmp 70 4 no ether1 36.6 86 -> 6C:3B:6B:ED:81:7D 6C:3B:6B:ED:83:63 172.24.24.1 172.24.24.2 ip:icmp 70 4 no
Traffic-Generator packets will not be visible using the packet sniffer on the same interface unless the fast-path parameter is set.
Packet Sniffer Protocols
In this submenu, you can see all sniffed protocols and their share of the whole sniffed amount.
[admin@MikroTik] /tool sniffer protocol> print # PROTOCOL IP-PROTOCOL PORT PACKETS BYTES SHARE 0 802.2 1 60 0.05% 1 ip 215 100377 99.04% 2 arp 2 120 0.11% 3 ipv6 6 788 0.77% 4 ip tcp 210 99981 98.65% 5 ip udp 3 228 0.22% 6 ip ospf 2 168 0.16% 7 ip tcp 8291 (winbox) 210 99981 98.65% 8 ip tcp 36771 210 99981 98.65% 9 ip udp 646 3 228 0.22%
Packet Sniffer Host
The submenu shows the list of hosts that were participating in data exchange you've sniffed.
[admin@MikroTik] /tool sniffer host> print # ADDRESS RATE PEEK-RATE TOTAL 0 10.5.101.3 0bps/0bps 0bps/720bps 0/90 1 10.5.101.10 0bps/0bps 175.0kbps/19.7kbps 61231/7011 2 10.5.101.13 0bps/0bps 0bps/608bps 0/76 3 10.5.101.14 0bps/0bps 0bps/976bps 0/212 4 10.5.101.15 0bps/0bps 19.7kbps/175.0kbps 7011/61231 5 224.0.0.2 0bps/0bps 608bps/0bps 76/0 6 224.0.0.5 0bps/0bps 1440bps/0bps 302/0
Packet Sniffer Connections
Here you can get a list of the connections that have been watched during the sniffing time.
[admin@MikroTik] tool sniffer connection> print Flags: A - active # SRC-ADDRESS DST-ADDRESS BYTES RESENDS MSS 0 A 10.0.0.241:1839 10.0.0.181:23 (telnet) 6/42 60/0 0/0 1 A 10.0.0.144:2265 10.0.0.181:22 (ssh) 504/252 504/0 0/0