...
Introduction
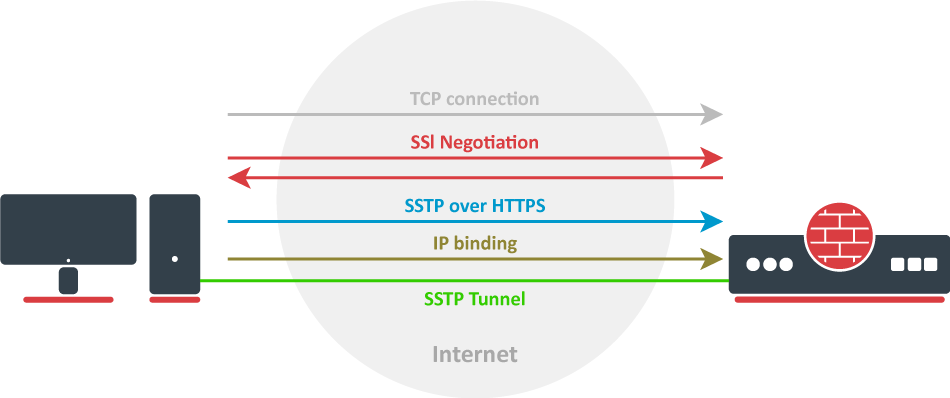
Let`s take a look at the SSTP connection mechanism:
- A TCP connection is established from client to server (by default on port 443);
- SSL validates the server certificate. If a certificate is valid, a connection is established otherwise the connection is turned down. (But see note below);
- The client sends SSTP control packets within the HTTPS session which establishes the SSTP state machine on both sides;
- PPP negotiation over SSTP. The client authenticates to the server and binds IP addresses to the SSTP interface;
SSTP tunnel is now established and packet encapsulation can begin;
| Note |
|---|
Starting from v5.0beta2 SSTP does not require certificates to operate and can use any available authentication type. This feature will work only between two MikroTik routers, as it is not in accordance with Microsoft standards. Otherwise to establish secure tunnels mschap authentication and client/server certificates from the same chain should be used. |
| Note |
|---|
TLS SNI support has been added starting with 7.15beta10 version, Extension will be added to client hello packets if "Add SNI" checkbox is checked or set in CLI: interface/sstp-client/set add-sni=yes |
Certificates
To set up a secure SSTP tunnel, certificates are required. On the server, authentication is done only by username and password, but on the client - the server is authenticated using a server certificate. It is also used by the client to cryptographically bind SSL and PPP authentication, meaning - the clients send a special value over SSTP connection to the server, this value is derived from the key data that is generated during PPP authentication and server certificate, this allows the server to check if both channels are secure.
...
- certificate is not yet valid - notBefore certificate date is after the current time;
- certificate has expired - certificate expiry date is before the current time;
- cinvalid certificate purpose - the supplied certificate cannot be used for the specified purpose;
- cself signed certificate in a chain - the certificate chain could be built up using the untrusted certificates but the root could not be found locally;
- cunable to get issuer certificate locally - CA certificate is not imported locally;
- cserver's IP address does not match certificate - server address verification is enabled, but the address provided in certificate does not match the server's address;
Quick Example
SSTP Client
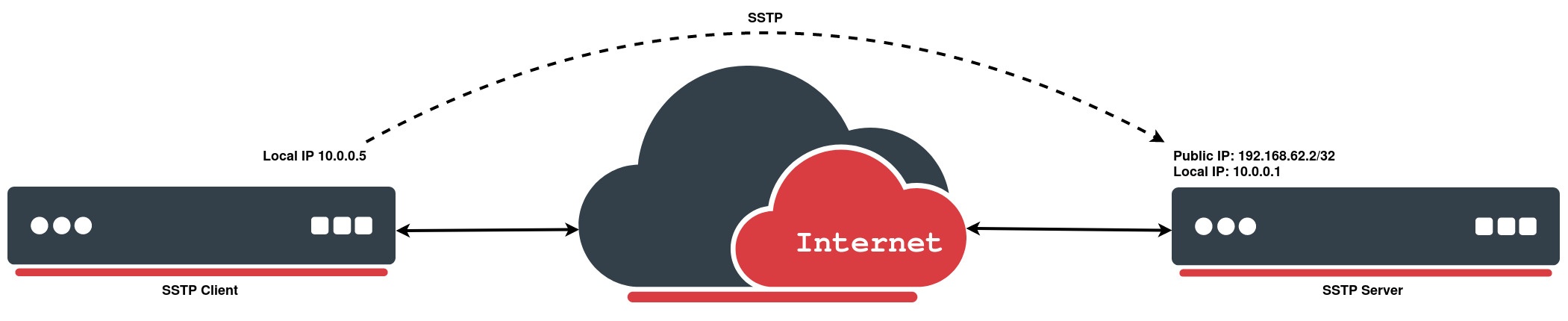
In the following configuration example, e will create a simple SSTP client without using a certificate:
| Code Block | ||
|---|---|---|
| ||
[admin@MikroTik > interface sstp-client add connect-to=192.168.62.2 disabled=no name=sstp-out1 password=StrongPass profile=default-encryption user=MT-User [admin@MikroTik > interface sstp-client print Flags: X - disabled; R - running 0 R name="sstp-out1" max-mtu=1500 max-mru=1500 mrru=disabled connect-to=192.168.62.2:443 http-proxy=0.0.0.0:443 certificate=none verify-server-certificate=no verify-server-address-from-certificate=yes user="MT-User" password="StrongPass" profile=default-encryption keepalive-timeout=60 add-default-route=no dial-on-demand=no authentication=pap,chap,mschap1,mschap2 pfs=no tls-version=any |
SSTP Server
We will configure PPP secret for a particular user, afterwards simply enable an SSTP server:
| Code Block | ||
|---|---|---|
| ||
[admin@MikroTik] > ppp secret add local-address=10.0.0.1 name=MT-User password=StrongPass remote-address=10.0.0.5 service=sstp
[admin@MikroTik] > interface sstp-server server set default-profile=default-encryption enabled=yes
[admin@MikroTik] > interface sstp-server server print
enabled: yes
port: 443
max-mtu: 1500
max-mru: 1500
mrru: disabled
keepalive-timeout: 60
default-profile: default-encryption
authentication: pap,chap,mschap1,mschap2
certificate: none
verify-client-certificate: no
pfs: no
tls-version: any |