...
| Property | Description |
|---|---|
| comment (string; Default: ) | Short description of the tunnel. |
| disabled (yes | no; Default: no) | Enables/disables the tunnel. |
| listen-port (integer; Default: 13231) | Port for WireGuard service to listen on for incoming sessions. |
| mtu (integer [0..65536]; Default: 1420) | Layer3 Maximum transmission unit. |
| name (string; Default: ) | Name of the tunnel. |
| private-key (string; Default: ) | A base64 private key. If not specified, it will be automatically generated upon interface creation. Each network interface has a private key and a list of peers. |
Read-only properties
| Property | Description |
|---|---|
| public-key (string) | A base64 public key is calculated from the private key. Each peer has a public key. Public keys are used by peers to authenticate each other. They can be passed around for use in configuration files. |
| running (yes | no) | Whether the interface is running. |
...
| Property | Description |
|---|---|
| allowed-address (IP/IPv6 prefix; Default: ) | List of IP (v4 or v6) addresses with CIDR masks from which incoming traffic for this peer is allowed and to which outgoing traffic for this peer is directed. The catch-all 0.0.0.0/0 may be specified for matching all IPv4 addresses, and ::/0 may be specified for matching all IPv6 addresses. |
| comment (string; Default: ) | Short description of the peer. |
| disabled (yes | no; Default: no) | Enables/disables the peer. |
| This IP address has to be in the same subnet as WireGuard interface set on ROS. If WireGuard interface is at 192.168.99.1/24, You have to input 192.168.99.2 to the client. By adding this IP under 'Allowed Address', you are saying that only this specific client (phone for example) is permitted to connect to this peer configuration. Allowed-address range cannot overlap on one interface, so you need to set own range for each peer. | |
| comment (string; Default: ) | Short description of the peer. |
| disabled (yes | no; Default: no) | Enables/disables the peer. |
| endpoint-address (IP/Hostname; Default: ) | The IP address or hostname. It is used by WireGuard to establish a secure connection between two peers. |
| endpoint-port (integer:0..65535; Default: ) | The Endpoint port is the UDP port on which a WireGuard peer listens for incoming traffic. |
| interface (string; Default: ) | Name of the WireGuard interface the peer belongs to. |
| persistent-keepalive (integer:0..65535; Default: 0) | A seconds interval, between 1 and 65535 inclusive, of how often to send an authenticated empty packet to the peer for the purpose of keeping a stateful firewall or NAT mapping valid persistently. For example, if the interface very rarely sends traffic, but it might at anytime receive traffic from a peer, and it is behind NAT, the interface might benefit from having a persistent keepalive interval of 25 seconds. |
| preshared-key (string; Default: ) | A base64 preshared key. Optional, and may be omitted. This option adds an additional layer of symmetric-key cryptography to be mixed into the already existing public-key cryptography, for post-quantum resistance. Also can be generated automatically or entered manually, when the key is provided by the system administrator. |
| private-key (auto/none; Default: none) | Can be generated automatically or entered manually, when the key is provided by the system administratorA base64 private key. |
public-key (string; Default: ) | The remote peer's calculated public key. It also can be generated if private-key is specifiedA base64 public key is calculated from the private key. Each peer has a public key. Public keys are used by peers to authenticate each other. They can be passed around for use in configuration files. |
show-client-config | Will show already created Peer configuration and generate a QR code for easier peer setup on a client device. Does not affect the WireGuard Server. |
Used for the client-server setup scenario, when the configuration is imported using a qr code for a client, configuration details on tab with qrcode will appear once it has been set in the fields: | |
client-address (IP/IPv6 prefix; Default: ) | When imported using a qr code for a client (for example, a phone), then this address for the wg interface is set on that device. |
client-dns (IP/IPv6 prefix; Default: ) | Specify when using WireGuard Server as a VPN gateway for peer traffic. |
client-endpoint (IP/IPv6 prefix; Default: ) | The IP address and port number of the WireGuard Server. |
client-keepalive (integer:0..65535; Default: 0) | Same as persistent-keepalive but from peer side. |
client-listen-port (integer:0..65535; Default: ) | The local port upon which this WireGuard tunnel will listen for incoming traffic from peers, and the port from which it will source outgoing packets. |
...
Minimum parameters must be specified for importing on the client device by QR-code/file.
...
interface: wireguard1 public-key: v/oIzPyFm1FPHrqhytZgsKjU7mUToQHLrW+Tb5e601M= private-key: KMwxqe/iXAU8Jn9dd1o5pPdHep2blGxNWm9I944/I24= allowed-address: 192.168.88.3/24 client-address: 192.168.88.3/32 client-endpoint: example.com:13231
...
name (string; Default: ) | Allows adding name to a peer. Name will be used as a reference for a peer in WireGuard logs. (Available from RouterOS version 7.15) |
is-responder (yes | no; Default: no) | Specifies if peer is intended to be connection initiator or only responder. Should be used on WireGuard devices that are used as "servers" for other devices as clients to connect to. Otherwise router will all repeatedly try to connect "endpoint-address" or "current-endpoint-address" causing unnecessary system logs to be written. |
*AllowedIPs configuration that is provided to the client through WireGuard peer export (configuration file or QR code) can not be changed and will be "0.0.0.0/0, ::/0" at the moment. If it is necessary to change these values on remote end, then that is up to the remote peer software used for WireGuard connection.
| Note |
|---|
Minimum parameters must be specified for importing on the client device by QR-code/file. Example: interface: wireguard1 public-key: v/oIzPyFm1FPHrqhytZgsKjU7mUToQHLrW+Tb5e601M= private-key: KMwxqe/iXAU8Jn9dd1o5pPdHep2blGxNWm9I944/I24= allowed-address: 192.168.88.3/24 client-address: 192.168.88.3/32 client-endpoint: example.com:13231 |
| Note |
|---|
When using interface/wireguard/wg-import file=, you may get Could not parse error, if Wireguard import file starts with #, use it clean as per example: [Interface] |
Read-only properties
| Property | Description |
|---|---|
| current-endpoint-address (IP/IPv6) | The most recent source IP address of correctly authenticated packets from the peer. |
| current-endpoint-port (integer) | The most recent source IP port of correctly authenticated packets from the peer. |
| last-handshake (integer) | Time in seconds after the last successful handshake. |
| rx (integer) | The total amount of bytes received from the peer. |
| tx (integer) | The total amount of bytes transmitted to the peer. |
Application examples
Site to Site WireGuard tunnel
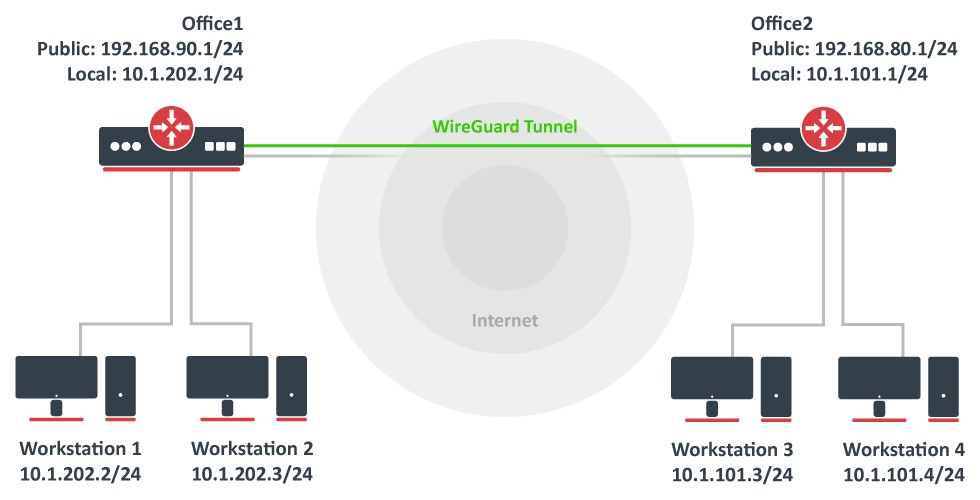
Consider setup as illustrated below. Two remote office routers are connected to the internet and office workstations are behind NAT. Each office has its own local subnet, 10.1.202.0/24 for Office1 and 10.1.101.0/24 for Office2. Both remote offices need secure tunnels to local networks behind routers.
WireGuard interface configuration
First of all, WireGuard interfaces must be configured on both sites to allow automatic private and public key generation. The command is the same for both routers:
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard
add listen-port=13231 name=wireguard1 |
Now when printing the interface details, both private and public keys should be visible to allow an exchange.
| Note |
|---|
Any private key will never be needed on the remote side device - hence the name private. |
Office1
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard print
Flags: X - disabled; R - running
|
Application examples
Site to Site WireGuard tunnel
Consider setup as illustrated below. Two remote office routers are connected to the internet and office workstations are behind NAT. Each office has its own local subnet, 10.1.202.0/24 for Office1 and 10.1.101.0/24 for Office2. Both remote offices need secure tunnels to local networks behind routers.
WireGuard interface configuration
First of all, WireGuard interfaces must be configured on both sites to allow automatic private and public key generation. The command is the same for both routers:
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard
add listen-port=13231 name=wireguard1 |
Now when printing the interface details, both private and public keys should be visible to allow an exchange.
| Note |
|---|
Any private key will never be needed on the remote side device - hence the name private. |
Office1
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard print
Flags: X - disabled; R - running
0 R name="wireguard1" mtu=1420 listen-port=13231 private-key="yKt9NJ4e5qlaSgh48WnPCDCEkDmq+VsBTt/DDEBWfEo="
public-key="u7gYAg5tkioJDcm3hyS7pm79eADKPs/ZUGON6/fF3iI=" |
Office2
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard/print Flags: X - disabled; R - running 0 R name="wireguard1" mtu=1420 listen-port=13231 private-key="KMwxqe/iXAU8Jn9dd1o5pPdHep2blGxNWm9I944/I24yKt9NJ4e5qlaSgh48WnPCDCEkDmq+VsBTt/DDEBWfEo=" public-key="v/oIzPyFm1FPHrqhytZgsKjU7mUToQHLrW+Tb5e601Mu7gYAg5tkioJDcm3hyS7pm79eADKPs/ZUGON6/fF3iI=" |
Peer configuration
Peer configuration defines who can use the WireGuard interface and what kind of traffic can be sent over it. To identify the remote peer, its public key must be specified together with the created WireGuard interface.
Office1
Office2
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard/print
Flags: X - disabled; R - running
0 R name="wireguard1" mtu=1420 listen-port=13231 private-key="KMwxqe/iXAU8Jn9dd1o5pPdHep2blGxNWm9I944/I24="
| ||
| Code Block | ||
| ||
/interface/wireguard/peers add allowed-address=10.1.101.0/24 endpoint-address=192.168.80.1 endpoint-port=13231 interface=wireguard1 \ public-key="v/oIzPyFm1FPHrqhytZgsKjU7mUToQHLrW+Tb5e601M=" |
Peer configuration
Peer configuration defines who can use the WireGuard interface and what kind of traffic can be sent over it. To identify the remote peer, its public key must be specified together with the created WireGuard interface.
Office1Office2
| Code Block | ||
|---|---|---|
| ||
/interface/wireguard/peers add allowed-address=10.1.202101.0/24 endpoint-address=192.168.9080.1 endpoint-port=13231 interface=wireguard1 \ public-key="u7gYAg5tkioJDcm3hyS7pm79eADKPs/ZUGON6/fF3iIv/oIzPyFm1FPHrqhytZgsKjU7mUToQHLrW+Tb5e601M=" |
IP and routing configuration
Lastly, IP and routing information must be configured to allow traffic to be sent over the tunnel.
Office1
Office2
| Code Block | ||
|---|---|---|
| ||
/ip/address add address=10.255.255.1/30 interface=wireguard1 /ipwireguard/routepeers add dstallowed-address=10.1.101202.0/24 gateway=wireguard1 |
Office2
| Code Block | ||
|---|---|---|
| ||
/ip/address add address=10.255.255.2/30endpoint-address=192.168.90.1 endpoint-port=13231 interface=wireguard1 \ /ip/route add dst-address=10.1.202.0/24 gateway=wireguard1 |
Firewall considerations
The default RouterOS firewall will block the tunnel from establishing properly. The traffic should be accepted in the "input" chain before any drop rules on both sites.
public-key="u7gYAg5tkioJDcm3hyS7pm79eADKPs/ZUGON6/fF3iI=" |
IP and routing configuration
Lastly, IP and routing information must be configured to allow traffic to be sent over the tunnel.
Office1
| Code Block | ||
|---|---|---|
| ||
/ip/address
add address=10.255.255.1/30 interface=wireguard1
/ip/route
add dst-address=10.1.101.0/24 gateway=wireguard1 |
Office2Office1
| Code Block | ||
|---|---|---|
| ||
/ip/firewall/filteraddress add action=accept chain=input dst-port=13231 protocol=udp src-address=192.168.80.1 |
Office2
address=10.255.255.2/30 interface=wireguard1
/ip/route
add dst-address=10.1.202.0/24 gateway=wireguard1 |
Firewall considerations
The default RouterOS firewall will block the tunnel from establishing properly. The traffic should be accepted in the "input" chain before any drop rules on both sites.
Office1
| Code Block | ||
|---|---|---|
| Code Block | ||
| ||
/ip/firewall/filter add action=accept chain=input dst-port=13231 protocol=udp src-address=192.168.9080.1 |
Office2
| Code Block | ||
|---|---|---|
| ||
/ip/firewall/filter
add action=accept chain=input dst-port=13231 protocol=udp src-address=192.168.90.1 |
Additionally, it is possible that the "forward" chain Additionally, it is possible that the "forward" chain restricts the communication between the subnets as well, so such traffic should be accepted before any drop rules as well.
...
"Allowed IPs" are set to 0.0.0.0/0 to allow all traffic to be sent over the WireGuard tunnel.
| Code Block | ||
|---|---|---|
| ||
Depending on your configuration, you may need to add a NAT rule
chain=dstnat action=dst-nat to-ports=port protocol=udp in-interface=interface dst-port=port |
Windows 10 configuration
Download WireGuard installer from Wireguard
Run as Administrator.
...