...
Network Address Translation is an Internet standard that allows hosts on local area networks to use one set of IP addresses for internal communications and another set of IP addresses for external communications. A LAN that uses NAT is ascribed as a natted network. For NAT to function, there should be a NAT gateway in each natted network. The NAT gateway (NAT router) performs IP address rewriting on the way packet while packets travel from/to LAN.
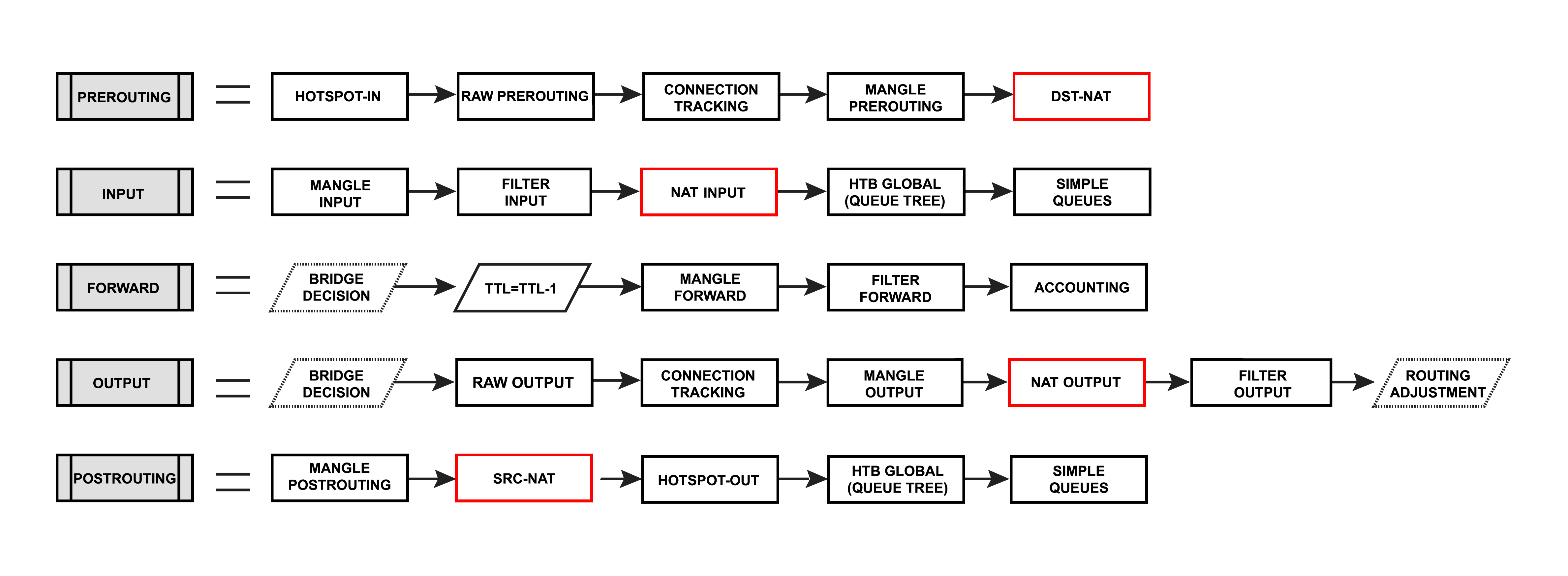
Nat matches only the first packet of the connection, connection tracking remembers the action and performs on all other packets belonging to the same connection.
| Warning |
|---|
Whenever NAT rules are changed or added, the connection tracking table should be cleared otherwise NAT rules may seem to be not functioning correctly until the connection entry expires. |
Types of NAT:
- source NAT or srcnat. This type of NAT is performed on packets that are originated from a natted network. A NAT router replaces the private source address of an IP packet with a new public IP address as it travels through the router. A reverse operation is applied to the reply packets traveling in the other direction.
- destination NAT or dstnat. This type of NAT is performed on packets that are destined for the natted network. It is most commonly used to make hosts on a private network to be accessible from the Internet. A NAT router performing dstnat replaces the destination IP address of an IP packet as it travels through the router towards toward a private network.
Destination NAT
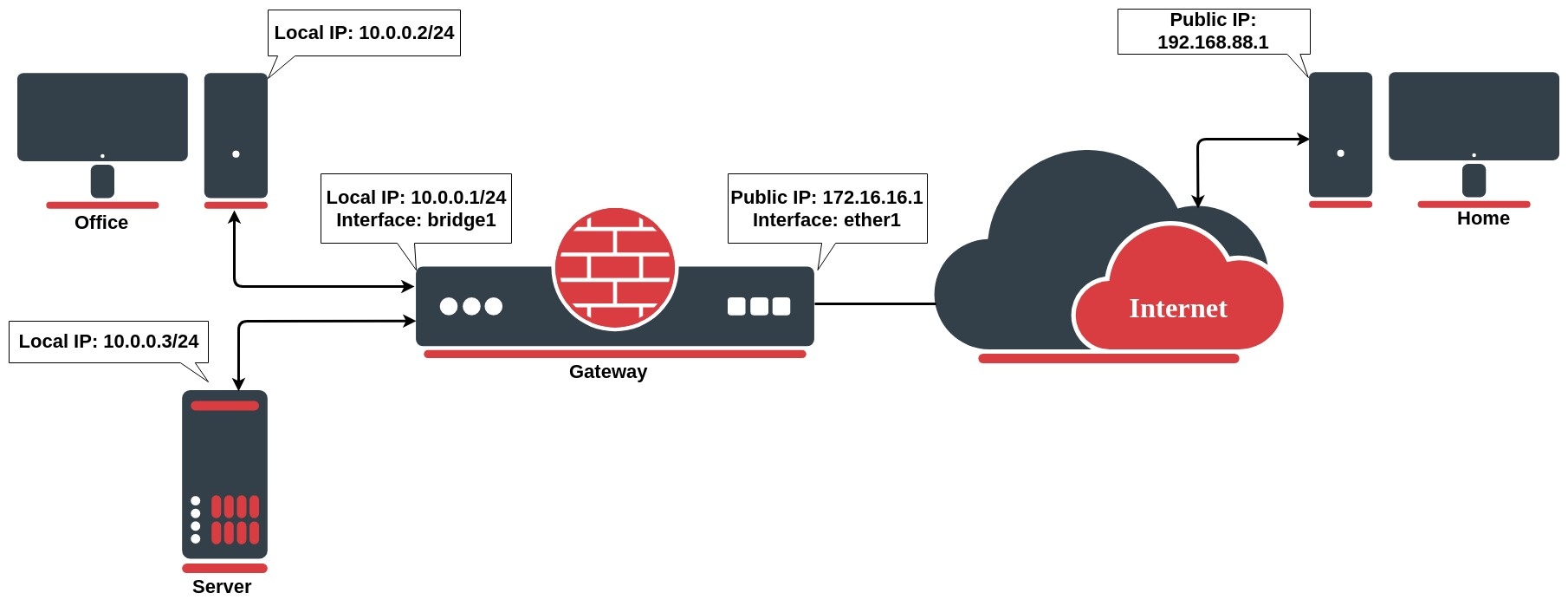
Network address translation works by modifying network address information in the packets IP header. Let`s take a look at the common setup where a network administrator wants to access an office server from the internet.
We want to allow connections from the internet to the office server whose local IP is 10.0.0.3. In this case, we have to configure a destination address translation rule on the office gateway router:
Since RouterOS v7 the firewall NAT has two new INPUT and OUTPUT chains which are traversed for packets delivered to and sent from applications running on the local machine:
- input - used to process packets entering the router through one of the interfaces with the destination IP address which is one of the router's addresses. Packets passing through the router are not processed against the rules of the input chain.
- output - used to process packets that originated from the router and leave it through one of the interfaces. Packets passing through the router are not processed against the rules of the output chain.
Destination NAT
Network address translation works by modifying network address information in the packet's IP header. Let`s take a look at the common setup where a network administrator wants to access an office server from the internet.
We want to allow connections from the internet to the office server whose local IP is 10.0.0.3. In this case, we have to configure a destination address translation rule on the office gateway router:
| Code Block | ||
|---|---|---|
| ||
/ip | ||
| Code Block | ||
| ||
/ip firewall nat add chain=dstnat action=dst-nat dst-address=172.16.16.1 dst-port=22 to-addresses=10.0.0.3 protocol=tcp |
...
If you want to hide your local devices behind your public IP address received from the ISP, you should you should configure the source network address translation (masquerading) feature of the MikroTik router.
Let`s assume you want to hide both the office computer and server behind the public IP 172.16.16.1, the rule will look like the following one:
...
Now your ISP will see all the requests coming with IP 172.16.16.1 and they will not see your LAN network IP addresses.
Masquerade
Firewall NAT action=masqueradeis a unique subversion of action=srcnat, it was designed for specific use in situations when public IP can randomly change, for example, DHCP server change changes assigned IP or PPPoE tunnel after disconnect gets a different IP, in short - when public IP is dynamic.
| Code Block | ||
|---|---|---|
| ||
/ip firewall nat add chain=srcnat src-address=10.0.0.0/24 action=masquarademasquerade out-interface=WAN |
Every time when interface disconnects and/or its IP address changes, the router will clear all masqueraded connection tracking entries related to the interface, this way improving system recovery time after public IP change. If srcnat is used instead of masquerade, connection tracking entries remain and connections can simply resume after a link failure.
...
To overcome these limitations RouterOS includes a number of so-called NAT helpers, that enable NAT traversal for various protocols. When action=srcnat is used instead, connection tracking entries remain and connections can simply resume.
...
To combat IPv4 address exhaustion, a new RFC 6598 was deployed. The idea is to use shared 100.64.0.0/10 address space inside the carrier's network and performing perform NAT on the carrier's edge router to a single public IP or public IP range.
Because of the nature of such a setup, it is also called NAT444, as opposed to a NAT44 network for a 'normal' NAT environment, three different IPv4 address spaces are involved.
...
- 2.2.2.2 - public IP address,
- public_if - interface on providers provider's edge router connected to the internet
...
Service providers may be required to do logging log of MAPed addresses, in a large CGN deployed network that which may be a problem. Fortunately, RFC 7422 suggests a way to manage CGN translations in such a way as to significantly reduce the amount of logging required while providing traceability for abuse response.
RFC states that instead of logging each connection, CGNs could deterministically map customer private addresses (received on the customer-facing interface of the CGN, a.k.a., internal side) to public addresses extended with port ranges.
In RouterOS described algorithm can be done with few script functions. Let's take an That means that separate NAT rules have to be added to achieve individual mappings such as the ones seen in the below example:
| Inside IP | Outside IP/Port range |
| 100.64.10.1 | 2.2.2.2:20005000-20995199 |
| 100.64.10.2 | 2.2.2.2:21005200-21995399 |
| 100.64.10.3 | 2.2.2.2:22005400-22995599 |
| 100.64.10.4 | 2.2.2.2:23005600-23995799 |
| 100.64.10.5 | 2.2.2.2:24005800-2499 |
| 100.64.1.6 | 2.2.2.2:2500-2599 |
| 5999 |
Instead of writing the rules by hand, it is suggested to use a script instead. The following example could be adapted to any requirements of your setupInstead of writing NAT mappings by hand, we could write a function that adds such rules automatically.
| Code Block | ||
|---|---|---|
| ||
:global sqrt do={ ######## Adjustable values ######### :forlocal i from=0 to=$1 do={ :if (i * i > $1) do={ :return ($i - 1) } } } :global addNatRules do={ StartingAddress 100.64.0.1 :local ClientCount 5 :local AddressesPerClient 2 :local PublicAddress 2.2.2.2 :local StartingPort 5000 :local PortsPerAddress 200 #################################### # All client chain jump /ip firewall nat add chain=srcnat action=jump jump-target=xxxclients \ src-address="$($srcStart)$StartingAddress-$($srcStart$StartingAddress + $count ($ClientCount * $AddressesPerClient) - 1)" :local x [$sqrt $count] :local y $x :if ($x * $x = $count) do={ :set y ($x + 1) } :for i from=0 to=$xcurrentPort $StartingPort :for c from=1 to=$ClientCount do={ # Specific client chain jumps :if ($AddressesPerClient > 1) do={ /ip firewall nat add chain=xxxclients action=jump jump-target="xxx-$($i)client-$c" \ src-address="$($srcStart$StartingAddress + ($x$AddressesPerClient * $i ($c - 1)))-$($srcStart$StartingAddress + ($x$AddressesPerClient * ($i + 1)$c - 1))" } else={ :for i from=0 to=($count - 1) do={ /ip firewall nat add chain=clients action=jump jump-target="client-$c" \ :local prange src-address="$($portStart$StartingAddress + ($i$AddressesPerClient * $portsPerAddr))-$($portStart + (($i +$c - 1)))" * $portsPerAddr) - 1)"} /ip firewall nat# add chain="xxx-$($i / $x)" action=src-nat protocol=tcp src-address=($srcStart + $i) \ to-address=$toAddr to-ports=$prange Translation rules :for a from=1 to=$AddressesPerClient do={ /ip firewall nat add chain="xxx-$($i / $x)client-$c" action=src-nat protocol=udptcp \ src-address="$($srcStart$StartingAddress + $i) \ (($c -1) * $AddressesPerClient) + $a - 1)" to-address=$toAddr$PublicAddress to-ports=$prange } } |
After pasting the above script in the terminal function "addNatRules" is available. If we take our example, we need to map 6 shared network addresses to be mapped to 2.2.2.2 and each address uses a range of 100 ports starting from 2000. So we run our function:
| Code Block | ||
|---|---|---|
| ||
$addNatRules count=6 srcStart=100.64.1.1 toAddr=2.2.2.2 portStart=2000 portsPerAddr=100 |
Now you should be able to get a set of rules:
"$currentPort-$($currentPort + $PortsPerAddress - 1)"
/ip firewall nat add chain="client-$c" action=src-nat protocol=udp \
src-address="$($StartingAddress + (($c -1) * $AddressesPerClient) + $a - 1)" to-address=$PublicAddress to-ports="$currentPort-$($currentPort + $PortsPerAddress - 1)"
:set currentPort ($currentPort + $PortsPerAddress)
}
}
} |
The six local values can be adjusted and the script can be either simply pasted in the terminal or it can be stored in the system script section, in case the configuration needs to be regenerated later.
After execution, you should get a set of rules:
| Code Block | ||
|---|---|---|
| ||
[admin@MikroTik] > ip firewall nat print
Flags: X - disabled, I - invalid; D - dynamic
0 chain=srcnat action=jump jump-target=clients
src-address=100.64.0.1-100.64.0.10
1 chain=clients | ||
| Code Block | ||
| ||
[admin@rack1_b18_450] /ip firewall nat> print Flags: X - disabled, I - invalid, D - dynamic 0 chain=srcnat action=jump jump-target=xxx src-address=100.64.1.1-100.64.1.6 log=no log-prefix="" 1 chain=xxx action=jump jump-target=xxx-0 src-address=100.64.1.1-100.64.1.2 log=no log-prefix="" 2 chain=xxx action=jump jump-target=xxx-1 src-address=100.64.1.3-100.64.1.4 log=no log-prefix="" 3 chain=xxx action=jump jump-target=xxx-2client-1 src-address=100.64.0.1.5-100.64.1.6 log=no log-prefix=""0.2 42 chain=xxxclient-01 action=src-nat to-addresses=2.2.2.2 to-ports=2000-20995000-5199 protocol=tcp src-address=100.64.10.1 log=no log-prefix="" 53 chain=xxxclient-01 action=src-nat to-addresses=2.2.2.2 to-ports=2000-20995000-5199 protocol=udp src-address=100.64.10.1 log=no log-prefix="" 64 chain=xxxclient-01 action=src-nat to-addresses=2.2.2.2 to-ports=2100-21995200-5399 protocol=tcp src-address=100.64.10.2 log=no log-prefix="" 75 chain=xxxclient-01 action=src-nat to-addresses=2.2.2.2 to-ports=21005200-21995399 protocol=udp protocol=udp src-address=100.64.10.2 log=no log-prefix="" 86 chain=xxx-1clients action=src-natjump tojump-addressestarget=2.2.2.2 to-ports=2200-2299 protocol=tcpclient-2 src-address=100.64.10.3 log=no log-prefix=""-100.64.0.4 97 chain=xxxclient-12 action=src-nat to-addresses=2.2.2.2 to-ports=2200-22995400-5599 protocol=udptcp src-address=100.64.10.3 log=no log-prefix="" 10 8 chain=xxxclient-12 action=src-nat to-addresses=2.2.2.2 to-ports=2300-23995400-5599 protocol=tcpudp src-address=100.64.1.4 log=no log-prefix=""0.3 11 9 chain=xxxclient-12 action=src-nat to-addresses=2.2.2.2 to-ports=2300-23995600-5799 protocol=udptcp src-address=100.64.10.4 log=no log-prefix="" 1210 chain=xxxclient-2 action=src-nat to-addresses=2.2.2.2 to-ports=2400-24995600-5799 protocol=tcpudp src-address=100.64.1.5 log=no log-prefix="" 130.4 11 chain=clients action=jump jump-target=client-3 src-address=100.64.0.5-100.64.0.6 12 chain=xxxclient-23 action=src-nat to-addresses=2.2.2.2 to-ports=2400-24995800-5999 protocol=udptcp src-address=100.64.10.5 log=no log-prefix="" 1413 chain=xxxclient-23 action=src-nat to-addresses=2.2.2.2 to-ports=2500-25995800-5999 protocol=tcpudp src-address=100.64.1.6 log=no log-prefix="".0.5 14 chain=client-3 action=src-nat to-addresses=2.2.2.2 to-ports=6000-6199 protocol=tcp src-address=100.64.0.6 15 chain=xxxclient-23 action=src-nat to-addresses=2.2.2.2 to-ports=2500-25996000-6199 protocol=udp src-address=100.64.10.6 log=no log-prefix="" [...] |
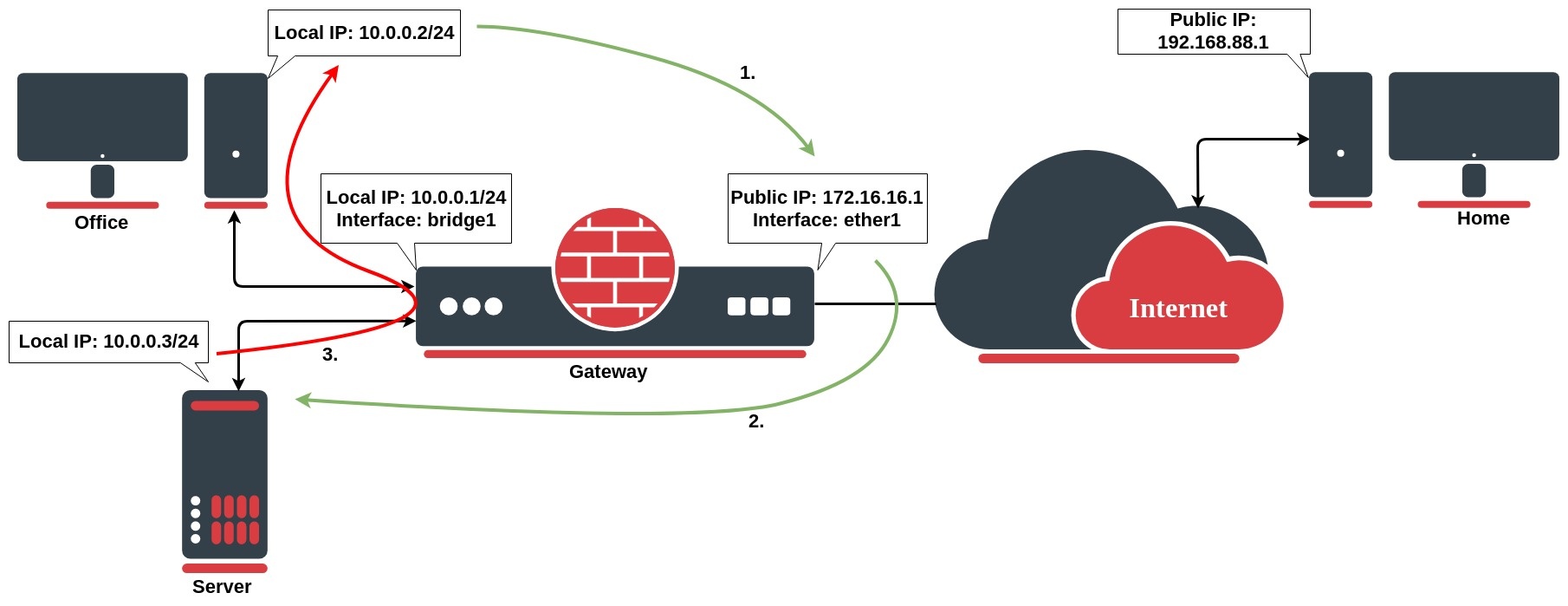
Hairpin NAT
Hairpin network address translation (NAT Loopback) is where the device on the LAN is able to LAN can access another machine on the LAN via the public IP address of the gateway router.
In the following above example, the gateway router consist of has the following dst-nat configuration rule:
| Code Block | ||
|---|---|---|
| ||
/ip firewall nat add chain=dstnat action=dst-nat dst-address=172.16.16.1 dst-port=443 to-addresses=10.0.0.3 to-ports=443 protocol=tcp |
When a customer user from the PC at home establishes a connection to the webserver, the router performs NAT as configured:
- the client sends a packet with a source IP address of 192.168.88.1 to a destination IP address of 172.16.16.1 on port 443 to request some web resource;
- the router destination NAT`s the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 192.168.88.1;
- the server replies to the client's request and the reply packet have a source IP address of 10.0.0.3 and a destination IP address of 192.168.88.1.
- the router determines that the packet is part of a previous connection and undoes the destination NAT, and puts the original destination IP address into the source IP address field. The destination IP address is 192.168.88.1, and the source IP address is 172.16.16.1;
- The client receives the reply packet it expects, and the connection is established;
The issue occurs, when a client on the same internal network as the webserver requests a connection to the web server's public IP address, the connection breaks:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resource;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 10.0.0.2;
- the server replies to the client's request. However, the source IP address of the request is on the same subnet as the webserver. The web server does not send the reply back to the router but sends it back directly to 10.0.0.2 with a source IP address in the reply of 10.0.0.3;
- The client receives the reply packet, but it discards it because it expects a packet back from 172.16.16.1, and not from 10.0.0.3;
To resolve this issue, we will configure the src-nat rule as follows:
| Code Block | ||
|---|---|---|
| ||
/ip firewall nat
add action=masquerade chain=srcnat dst-address=10.0.0.3 out-interface=LAN protocol=tcp src-address=10.0.0.0/24 |
After configured rule above:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resource;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. It also source NATs the packet and replaces the source IP address in the packet with the IP address on its LAN interface. The destination IP address is 10.0.0.3, and the source IP address is 10.0.0.1;
- the webserver replies to the request and sends the reply with a source IP address of 10.0.0.3 back to the router's LAN interface IP address of 10.0.0.1;
- the router determines that the packet is part of a previous connection and undoes both the source and destination NAT, and puts the original destination IP address of 1.1.1.1 into the source IP address field, and the original source IP address of 172.16.16.1 into the destination IP address field
Properties
web server, the router performs DST NAT as configured:
- the client sends a packet with a source IP address of 192.168.88.1 to a destination IP address of 172.16.16.1 on port 443 to request some web resources;
- the router destination NAT`s the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 192.168.88.1;
- the server replies to the client's request and the reply packet has a source IP address of 10.0.0.3 and a destination IP address of 192.168.88.1.
- the router determines that the packet is part of a previous connection and undoes the destination NAT, and puts the original destination IP address into the source IP address field. The destination IP address is 192.168.88.1, and the source IP address is 172.16.16.1;
- The client receives the reply packet it expects, and the connection is established;
But, there will be a problem, when a client on the same network as the web server requests a connection to the web server's public IP address:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resources;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 10.0.0.2;
- the server replies to the client's request. However, the source IP address of the request is on the same subnet as the web server. The web server does not send the reply back to the router but sends it back directly to 10.0.0.2 with a source IP address in the reply of 10.0.0.3;
- The client receives the reply packet, but it discards it because it expects a packet back from 172.16.16.1, and not from 10.0.0.3;
To resolve this issue, we will configure a new src-nat rule (the hairpin NAT rule) as follows:
| Code Block | ||
|---|---|---|
| ||
/ip firewall nat
add action=masquerade chain=srcnat dst-address=10.0.0.3 out-interface=LAN protocol=tcp src-address=10.0.0.0/24 |
After configuring the rule above:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resources;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. It also source NATs the packet and replaces the source IP address in the packet with the IP address on its LAN interface. The destination IP address is 10.0.0.3, and the source IP address is 10.0.0.1;
- the web server replies to the request and sends the reply with a source IP address of 10.0.0.3 back to the router's LAN interface IP address of 10.0.0.1;
- the router determines that the packet is part of a previous connection and undoes both the source and destination NAT, and puts the original destination IP address of 10.0.0.3 into the source IP address field, and the original source IP address of 172.16.16.1 into the destination IP address field
Endpoint-Independent NAT
Endpoint-independent NAT creates mapping in the source NAT and uses the same mapping for all subsequent packets with the same source IP and port. This mapping is created with the following rule:
| Code Block | ||
|---|---|---|
| ||
/ip firewall nat
add action=endpoint-independent-nat chain=srcnat out-interface=WAN protocol=udp |
This mapping allows running source-independent filtering, which allows forwarding packets from any source from WAN to mapped internal IP and port. The following rule enables filtering:
| Code Block | ||
|---|---|---|
| ||
/ip firewall nat
add action=endpoint-independent-nat chain=dstnat in-interface=WAN protocol=udp |
| Note |
|---|
Endpoint-independent NAT works only with UDP protocol. |
Additionally, endpoint-independent-nat can take a few other parameters:
randomize-port- randomize to which public port connections will be mapped.
More info https://www.ietf.org/rfc/rfc5128.txt section 2.2.3 and 2.2.5
IPv4
Properties
| Property | Description |
|---|---|
| action (action name; Default: accept) | Action to take if a packet is matched by the rule:
|
| address-list (string; Default: ) | Name of the address list to be used. Applicable if action is add-dst-to-address-list or add-src-to-address-list |
| address-list-timeout (none-dynamic | none-static | time; Default: none-dynamic) | Time interval after which the address will be removed from the address list specified by address-list parameter. Used in conjunction with add-dst-to-address-list or add-src-to-address-list actions
|
| chain (name; Default: ) | Specifies to which chain rule will be added. If the input does not match the name of an already defined chain, a new chain will be created |
| comment (string; Default: ) | Descriptive comment for the rule |
| connection-bytes (integer-integer; Default: ) | Matches packet only if a given amount of bytes has been transferred through the particular connection. 0 - means infinity, for example connection-bytes=2000000-0 means that the rule matches if more than 2MB has been transferred through the relevant connection |
| connection-limit (integer,netmask; Default: ) | Matches connections per address or address block after a given value is reached |
| connection-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular connection mark. If a no-mark is set, the rule will match any unmarked connection |
| connection-rate (Integer 0..4294967295; Default: ) | Connection Rate is a firewall matcher that allows capturing traffic based on the present speed of the connection |
| connection-type (ftp | h323 | irc | pptp | quake3 | sip | tftp; Default: ) | Matches packets from related connections based on information from their connection tracking helpers. A relevant connection helper must be enabled under /ip firewall service-port |
| content (string; Default: ) | Match packets that contain specified text |
| dscp (integer: 0..63; Default: ) | Matches DSCP IP header field. |
| dst-address (IP/netmask | IP range; Default: ) | Matches packets whose destination is equal to a specified IP or falls into a specified IP range. |
| dst-address-list (name; Default: ) | Matches the destination address of a packet against a user-defined address list |
| dst-address-type (unicast | local | broadcast | multicast; Default: ) | Matches destination address type:
|
| dst-limit (integer[/time],integer,dst-address | dst-port | src-address[/time]; Default: ) | Matches packets until a given PPS limit is exceeded. As opposed to the limit matcher, every destination IP address/destination port has its own limit. Parameters are written in the following format: count[/time],burst,mode[/expire].
|
| dst-port (integer[-integer]: 0..65535; Default: ) | List of destination port numbers or port number ranges in format Range[,Port], for example, dst-port=123-345,456-678 |
| fragment (yes|no; Default: ) | Matches fragmented packets. The first (starting) fragment does not count. If connection tracking is enabled there will be no fragments as the system automatically assembles every packet |
| hotspot (auth | from-client | http | local-dst | to-client; Default: ) | Matches packets received from HotSpot clients against various HotSpot matchers.
|
| icmp-options (integer:integer; Default: ) | Matches ICMP type: code fields |
| in-bridge-port (name; Default: ) | Actual interface the packet has entered the router if the incoming interface is a bridge |
| in-interface (name; Default: ) | Interface the packet has entered the router |
| ingress-priority (integer: 0..63; Default: ) | Matches ingress the priority of the packet. Priority may be derived from VLAN, WMM or MPLS EXP bit. |
| ipsec-policy (in | out, ipsec | none; Default: ) | Matches the policy used by IPSec. Value is written in the following format: direction, policy. The direction is Used to select whether to match the policy used for decapsulation or the policy that will be used for encapsulation.
For example, if a router receives an IPsec encapsulated Gre packet, then the rule |
| ipv4-options (any | loose-source-routing | no-record-route | no-router-alert | no-source-routing | no-timestamp | none | record-route | router-alert | strict-source-routing | timestamp; Default: ) | Matches IPv4 header options.
|
| jump-target (name; Default: ) | Name of the target chain to jump to. Applicable only if action=jump |
| layer7-protocol (name; Default: ) | Layer7 filter name defined in layer7 protocol menu. |
| limit (integer,time,integer; Default: ) | Matches packets until a given PPS limit is exceeded. Parameters are written in the following format: count[/time],burst.
|
| log (yes | no; Default: no) | Add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port, and length of the packet. |
| log-prefix (string; Default: ) | Adds specified text at the beginning of every log message. Applicable if action=log or log=yes configured. |
| out-bridge-port (name; Default: ) | Actual interface the packet is leaving the router if the outgoing interface is a bridge |
| out-interface (; Default: ) | Interface the packet is leaving the router |
| packet-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular packet mark. If no-mark is set, the rule will match any unmarked packet |
| packet-size (integer[-integer]:0..65535; Default: ) | Matches packets of specified size or size range in bytes |
| per-connection-classifier (ValuesToHash:Denominator/Remainder; Default: ) | PCC matcher allows dividing traffic into equal streams with the ability to keep packets with a specific set of options in one particular stream |
| port (integer[-integer]: 0..65535; Default: ) | Matches if any (source or destination) port matches the specified list of ports or port ranges. Applicable only if protocol is TCP or UDP |
| protocol (name or protocol ID; Default: tcp) | Matches particular IP protocol specified by protocol name or number |
| psd (integer,time,integer,integer; Default: ) | Attempts to detect TCP and UDP scans. Parameters are in the following format WeightThreshold, DelayThreshold, LowPortWeight, HighPortWeight
|
| random (integer: 1..99; Default: ) | Matches packets randomly with a given probability |
| routing-mark (string; Default: ) | Matches packets marked by mangle facility with particular routing mark |
| same-not-by-dst (yes | no; Default: ) | Specifies whether to take into account or not the destination IP address when selecting a new source IP address. Applicable if action=same |
| src-address (Ip/Netmaks, Ip range; Default: ) | Matches packets whose source is equal to a specified IP or falls into a specified IP range. |
| src-address-list (name; Default: ) | Matches the source address of a packet against a user-defined address list |
| src-address-type (unicast | local | broadcast | multicast; Default: ) | Matches source address type:
|
| src-port (integer[-integer]: 0..65535; Default: ) | List of source ports and ranges of source ports. Applicable only if a protocol is TCP or UDP. |
| src-mac-address (MAC address; Default: ) | Matches the source MAC address of the packet |
| tcp-mss (integer[-integer]: 0..65535; Default: ) | Matches the TCP MSS value of an IP packet |
| time (time-time,sat | fri | thu | wed | tue | mon | sun; Default: ) | Allows to create a filter based on the packets' arrival time and date or, for locally generated packets, departure time and date |
| to-addresses (IP address[-IP address]; Default: 0.0.0.0) | Replace the original address with the specified one. Applicable if action is dst-nat, netmap, same, src-nat |
| to-ports (integer[-integer]: 0..65535; Default: ) | Replace the original port with the specified one. Applicable if action is dst-nat, redirect, masquerade, netmap, same, src-nat |
| ttl (integer: 0..255; Default: ) | Matches packet's TTL value |
Stats
| Property | Description |
|---|---|
| bytes (integer) | The total amount of bytes matched by the rule |
| packets (integer) | The total amount of packets matched by the rule |
To show additional read-only properties:
| Code Block | ||
|---|---|---|
| ||
[admin@MikroTik] > ip firewall nat print stats all
Flags: X - disabled, I - invalid, D - dynamic
# CHAIN ACTION BYTES PACKETS
0 srcnat masquerade 265 659 987 |
IPv6
NAT66 is supported since RouterOS v7.1.
| Code Block | ||
|---|---|---|
| ||
ipv6/firewall/nat/ |
Properties
| Property | Description | |||
|---|---|---|---|---|
| action (action name; Default: accept) | Action to take if a packet is matched by the rule:
| |||
| Property | Description | |||
| action (action name; Default: accept) | Action to take if a packet is matched by the rule:
| |||
| address-list (string; Default: ) | Name of the address list to be used. Applicable if action is add-dst-to-address-list or add-src-to-address-list | |||
| address-list-timeout (none-dynamic | none-static | time; Default: none-dynamic) | Time interval after which the address will be removed from the address list specified by address-list parameter. Used in conjunction with add-dst-to-address-list or add-src-to-address-list actions
| |||
| chain (name; Default: ) | Specifies to which chain rule will be added. If the input does not match the name of an already defined chain, a new chain will be created | |||
| comment (string; Default: ) | Descriptive comment for the rule | |||
| connection-bytes (integer-integer; Default: ) | Matches packets only if a given amount of bytes has been transferred through the particular connection. 0 - means infinity, for example connection-bytes=2000000-0 means that the rule matches if more than 2MB has been transferred through the relevant connection | |||
| connection-limit (integer,netmask; Default: ) | Matches connections per address or address block after a given value is reached | |||
| connection-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular connection mark. If no-mark is set, the rule will match any unmarked connection | |||
| address-list (string; Default: ) | Name of the address list to be used. Applicable if action is add-dst-to-address-list or add-src-to-address-list | |||
| address-list-timeout (none-dynamic | none-static | time; Default: none-dynamic) | Time interval after which the address will be removed from the address list specified by address-list parameter. Used in conjunction with add-dst-to-address-list or add-src-to-address-list actions
| |||
| chain (name; Default: ) | Specifies to which chain rule will be added. If the input does not match the name of an already defined chain, a new chain will be created | |||
| comment (string; Default: ) | Descriptive comment for the rule | |||
| connection-bytes (integer-integer; Default: ) | Matches packets only if a given amount of bytes has been transferred through the particular connection. 0 - means infinity, for example connection-bytes=2000000-0 means that the rule matches if more than 2MB has been transferred through the relevant connection | |||
| connection-limit (integer,netmask; Default: ) | Matches connections per address or address block after a given value is reached | |||
| connection-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular connection mark. If no-mark is set, the rule will match any unmarked connection | |||
| connection-rate (Integer 0..4294967295; Default: ) | Connection Rate is a firewall matcher that allows capturing traffic based on the present speed of the connection | |||
| connection-state (established | invalid | new | related | untracked; Default: ) | Interprets the connection tracking analytics data for a particular packet:
| connection-rate (Integer 0..4294967295; Default: ) | Connection Rate is a firewall matcher that allows capturing traffic based on the present speed of the connection||
| connection-type (ftp | h323 | irc | pptp | quake3 | sip | tftp; Default: ) | Matches packets from related connections based on information from their connection tracking helpers. A relevant connection helper must be enabled under /ip firewall service-port | |||
| content (string; Default: ) | Match packets that contain specified text | |||
| dscp (integer: 0..63; Default: ) | Matches DSCP IP header field. | |||
| dst-address (IP/netmask | IP range; Default: ) | Matches packets which whose destination is equal to a specified IP or falls into a specified IP range. | |||
| dst-address-list (name; Default: ) | Matches the destination address of a packet against a user-defined address list | |||
| dst-address-type (unicast | local | broadcast | multicast; Default: ) | Matches destination address type:
| |||
| address list | ||||
| dst-address-type (unicast | local | broadcast | multicastdst-limit (integer[/time],integer,dst-address | dst-port | src-address[/time]; Default: ) | Matches packets until a given pps limit is exceeded. As opposed to the limit matcher, every destination IP address/destination port has its own limit. Parameters are written in the following format: count[/time],burst,mode[/expire].
| |||
| dst-port (integer[-integer]: 0..65535; Default: ) | List of destination port numbers or port number ranges | |||
destination address type:
| ||||
| dst-limit (integer[/time],integer,dst-address | dst-port | src-address[/time]fragment (yes|no; Default: ) | Matches fragmented packets. The first (starting) fragment does not count. If connection tracking is enabled there will be no fragments as the system automatically assembles every packetpackets until a given PPS limit is exceeded. As opposed to the limit matcher, every destination IP address/destination port has its own limit. Parameters are written in the following format: count[/time],burst,mode[/expire].
| |||
| dst-port (integer[-integer]: 0..65535; Default: ) | List of destination port numbers or port number ranges in format Range[,Port], for example, dst-port=123-345,456-678 | hotspot (auth | from-client | http | local-dst | to-client; Default: ) | Matches packets received from HotSpot clients against various HotSpot matchers. | |
| icmp-options (integer:integer; Default: ) | Matches ICMP type: code fields | |||
| in-bridge-port (name; Default: ) | Actual interface the packet has entered the router if the incoming interface is a bridge | |||
| in-interface (name; Default: ) | Interface the packet has entered the router | |||
| ingress-priority (integer: 0..63; Default: ) | Matches ingress the priority of the packet. Priority may be derived from VLAN, WMM or MPLS EXP bit. | |||
| ipsec-policy (in | out, ipsec | nonebridge-port (name; Default: ) | Actual interface the packet has entered the router if the incoming interface is a bridge | |||
| in-bridge-port-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as in-bridge-port | |||
| in-interface (name; Default: ) | Interface the packet has entered the router | |||
| in-interface-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as in-interface | |||
| ingress-priority (integer: 0..63; Default: ) | Matches ingress the priority of the packet. Priority may be derived from VLAN, WMM or MPLS EXP bit. | |||
| ipsec-policy (in | out, ipsec | none; Default: ) | Matches the policy used by IPSec. Value is written in the following format: direction, policy. The direction is Used to select whether to match the policy used for decapsulation or the policy that will be used for encapsulation.
For example, if a router receives an IPsec encapsulated Gre packet, then the rule | Matches the policy used by IpSec. Value is written in the following format: direction, policy. The direction is Used to select whether to match the policy used for decapsulation or the policy that will be used for encapsulation.
For example, if a router receives an IPsec encapsulated Gre packet, then rule | ipv4-options (any | loose-source-routing | no-record-route | no-router-alert | no-source-routing | no-timestamp | none | record-route | router-alert | strict-source-routing | timestamp; Default: ) | Matches IPv4 header options. |
| jump-target (name; Default: ) | Name of the target chain to jump to. Applicable only if action=jump | |||
| layer7-protocol (name; Default: ) | Layer7 filter name defined in layer7 protocol menu. | |||
| limit (integer,time,integer; Default: ) | Matches packets until a given PPS limit is exceeded. Parameters are written in the following format: count[/time],burst.
| |||
| log-prefix (stringlog (yes | no; Default: no) | Add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port, and length of the packet. | |||
| log-prefix (string; Default: ) | Adds specified text at the beginning of every log message. Applicable if action=log or log=yes configured. | Adds specified text at the beginning of every log message. Applicable if action=log | nth (integer,integer; Default: ) | Matches every nth packet: nth=2,1 rule will match every first packet of 2, hence, 50% of all the traffic that is matched by the rule |
| out-bridge-port (name; Default: ) | Actual interface the packet is leaving the router if the outgoing interface is a bridge | |||
| out-bridge-port-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as out-bridge-port | |||
| out-interface (; Default: ) | Interface the packet is leaving the routerthe router | |||
| out-interface-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as out-interface | |||
| packet-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular packet mark. If no-mark is set, the rule will match any unmarked packet | |||
| packet-size (integer[-integer]:0..65535; Default: ) | Matches packets of specified size or size range in bytes | |||
| per-connection-classifier (ValuesToHash:Denominator/Remainder; Default: ) | PCC matcher allows dividing traffic into equal streams with the ability to keep packets with a specific set of options in one particular stream | |||
| port (integer[-integer]: 0..65535; Default: ) | Matches if any (source or destination) port matches the specified list of ports or port ranges. Applicable only if protocol is TCP or UDP | |||
| protocol (name or protocol ID; Default: tcp) | Matches particular IP protocol specified by protocol name or numberpsd | |||
| priority (integer | ,time,integer,integer: 0..63; Default:) | Attempts to detect TCP and UDP scans. Parameters are in the following formatMatches the packet's priority after a new priority has been set. Priority may be derived from VLAN, WMM, DSCP, MPLS EXP bit, or from the priority that has been set using the set-priority action. | ||
| random (integer: 1..99; Default: ) | Matches packets randomly with a given probability | |||
| routing-mark (string; Default: ) | Matches packets marked by mangle facility with particular routing mark | same-not-by-dst (yes | no; Default: ) | Specifies whether to take into account or not destination IP address when selecting a new source IP address. Applicable if action=same | |
| src-address (Ip/Netmaks, Ip range; Default: ) | Matches packets which whose source is equal to a specified IP or falls into a specified IP range. | |||
| src-address-list (name; Default: ) | Matches the source address of a packet against a user-defined address list | |||
| src-address-type (unicast | local | broadcast | multicast; Default: ) | Matches source address type:
| |||
| src-port (integer[-integer]: 0..65535; Default: ) | List of source ports and ranges of source ports. Applicable only if a protocol is TCP or UDP.a protocol is TCP or UDP. | |||
| tcp-flags (ack | cwr | ece | fin | psh | rst | syn | urg; Default: ) | Matches specified TCP flags
| |||
| src-mac-address (MAC address; Default: ) | Matches the source MAC address of the packet | |||
| tcp-mss (integer[-integer]: 0..65535; Default: ) | Matches the TCP MSS value of an IP packet | |||
| time (time-time,sat | fri | thu | wed | tue | mon | sun; Default: ) | Allows to create a filter based on the packets' arrival time and date or, for locally generated packets, departure time and date | |||
| to-addresses (IP address[-IP address]; Default: 0.0.0.0) | Replace the original address with the specified one. Applicable if action is dst-nat, netmap, same, src-nat | |||
| to-ports (integer[-integer]: 0..65535; Default: ) | Replace the original port with the specified one. Applicable if action is dst-nat, redirect, masquerade, netmap, same, src-nat | |||
| ttl (integer: 0..255; Default: ) | Matches packets TTL value |
Stats
| Property | Description |
|---|---|
| bytes (integer) | The total amount of bytes matched by the rule |
| packets (integer) | The total amount of packets matched by the rule |
To show additional read-only properties:
| Code Block | ||
|---|---|---|
| ||
[admin@MikroTik] > ip firewall nat print stats all Flags: X - disabled, I - invalid, D - dynamic # CHAIN ACTION BYTES PACKETS 0 srcnat masquerade 265 659 987ipv6/firewall/nat/print stats |