Introduction
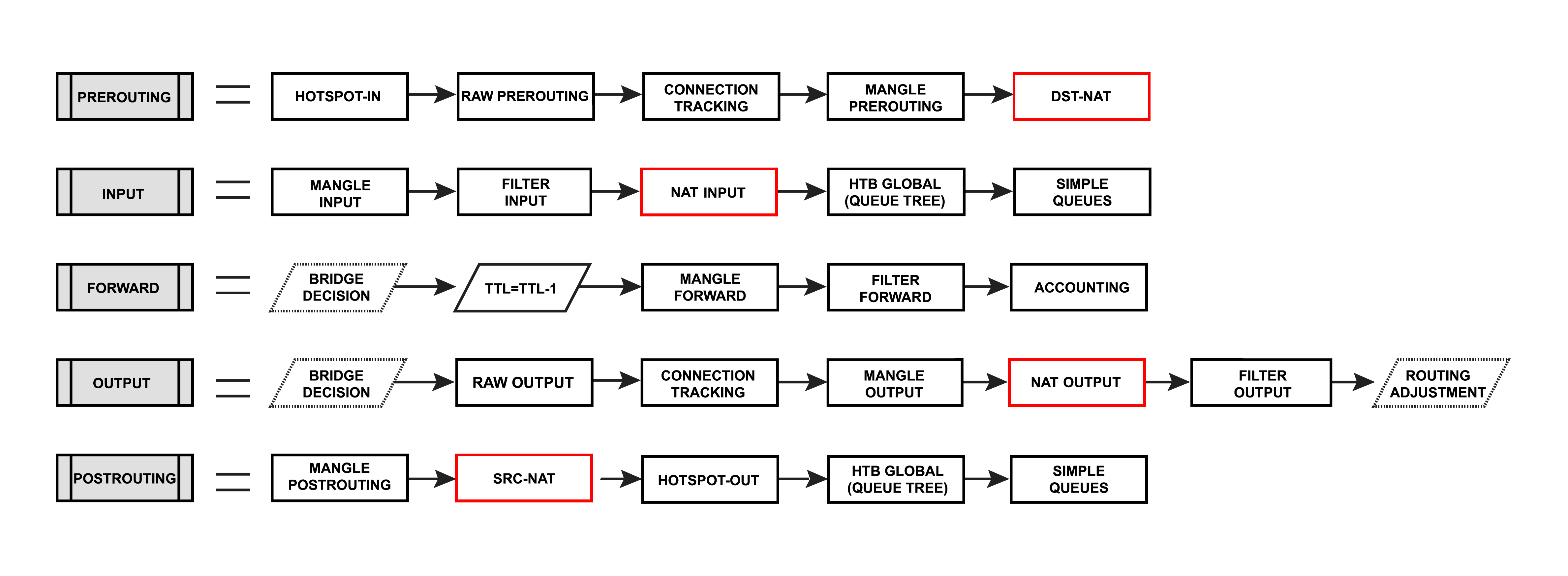
Network Address Translation is an Internet standard that allows hosts on local area networks to use one set of IP addresses for internal communications and another set of IP addresses for external communications. A LAN that uses NAT is ascribed as a natted network. For NAT to function, there should be a NAT gateway in each natted network. The NAT gateway (NAT router) performs IP address rewriting on the way packet while packets travel from/to LAN.
Nat matches only the first packet of the connection, connection tracking remembers the action and performs on all other packets belonging to the same connection.
| Warning |
|---|
Whenever NAT rules are changed or added, the connection tracking table should be cleared otherwise NAT rules may seem to be not functioning correctly until the connection entry expires. |
Types of NAT:
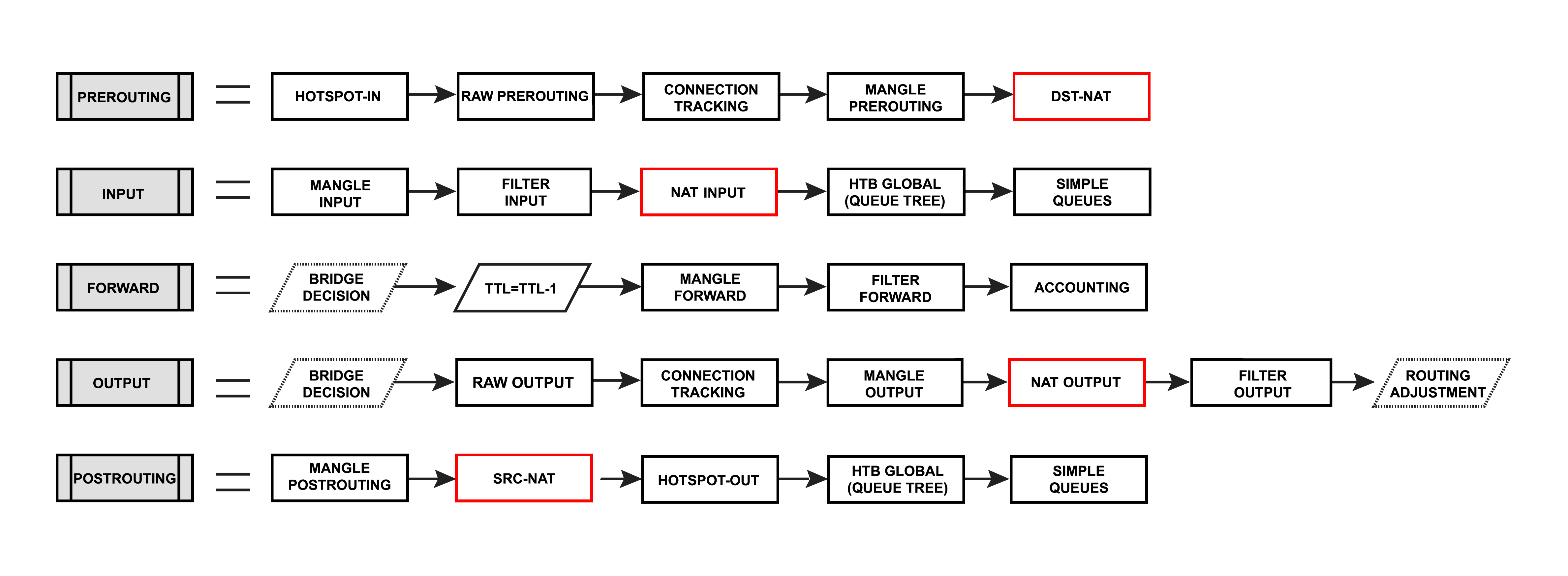 Image Modified
Image Modified
- source NAT or srcnat. This type of NAT is performed on packets that are originated from a natted network. A NAT router replaces the private source address of an IP packet with a new public IP address as it travels through the router. A reverse operation is applied to the reply packets traveling in the other direction.
- destination NAT or dstnat. This type of NAT is performed on packets that are destined for the natted network. It is most commonly used to make hosts on a private network to be accessible from the Internet. A NAT router performing dstnat replaces the destination IP address of an IP packet as it travels through the router towards toward a private network.
Destination NAT
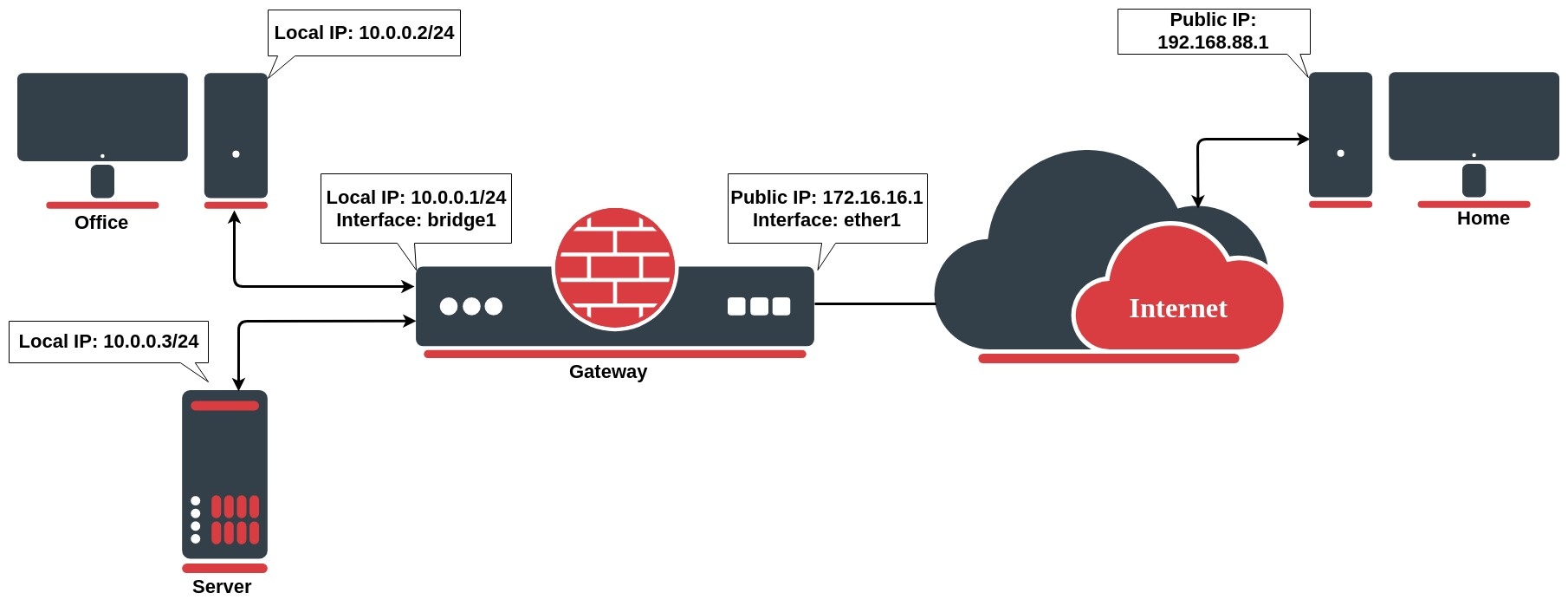 Image Removed
Image Removed
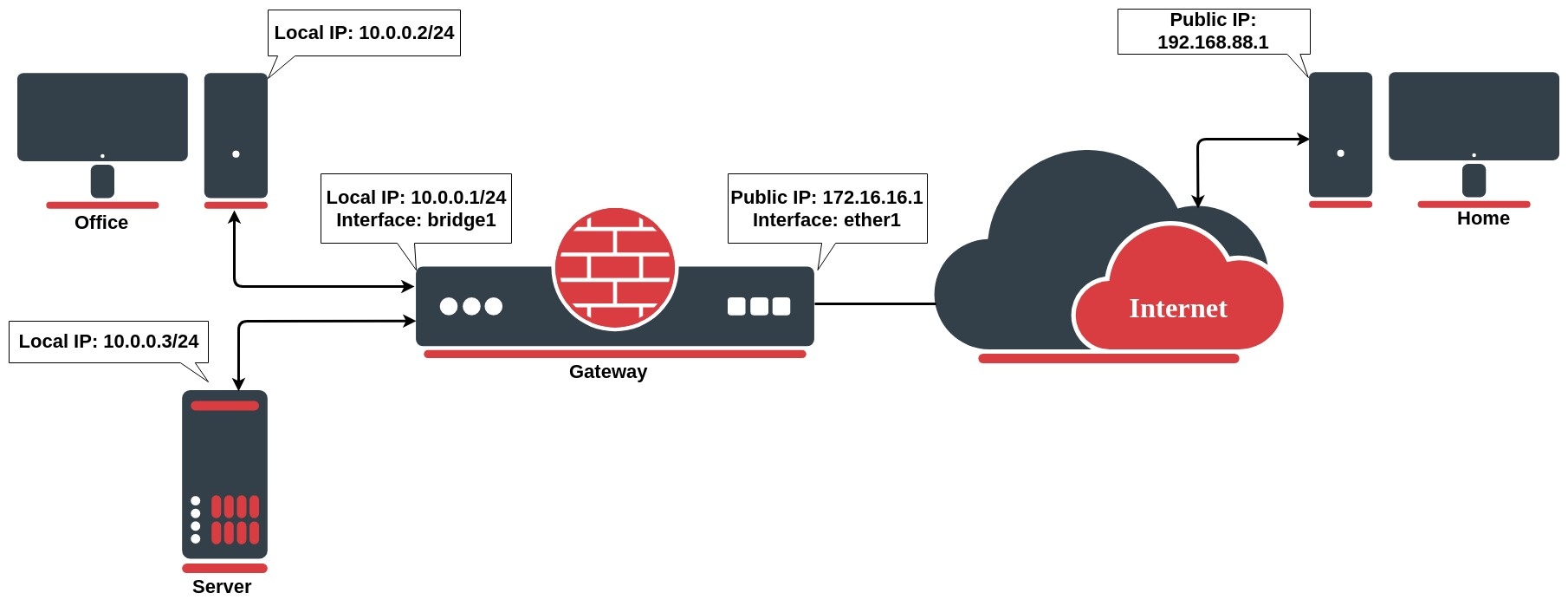
Network address translation works by modifying network address information in the packets IP header. Let`s take a look at the common setup where a network administrator wants to access an office server from the internet.
We want to allow connections from the internet to the office server whose local IP is 10.0.0.3. In this case, we have to configure a destination address translation rule on the office gateway router:
| Code Block |
|---|
|
/ip firewall nat add chain=dstnat action=dst-nat dst-address=172.16.16.1 dst-port=22 to-addresses=10.0.0.3 protocol=tcp |
...
Since RouterOS v7 the firewall NAT has two new INPUT and OUTPUT chains which are traversed for packets delivered to and sent from applications running on the local machine:
- input - used to process packets entering the router through one of the interfaces with the destination IP address which is one of the router's addresses. Packets passing through the router are not processed against the rules of the input chain.
- output - used to process packets that originated from the router and leave it through one of the interfaces. Packets passing through the router are not processed against the rules of the output chain.
Destination NAT
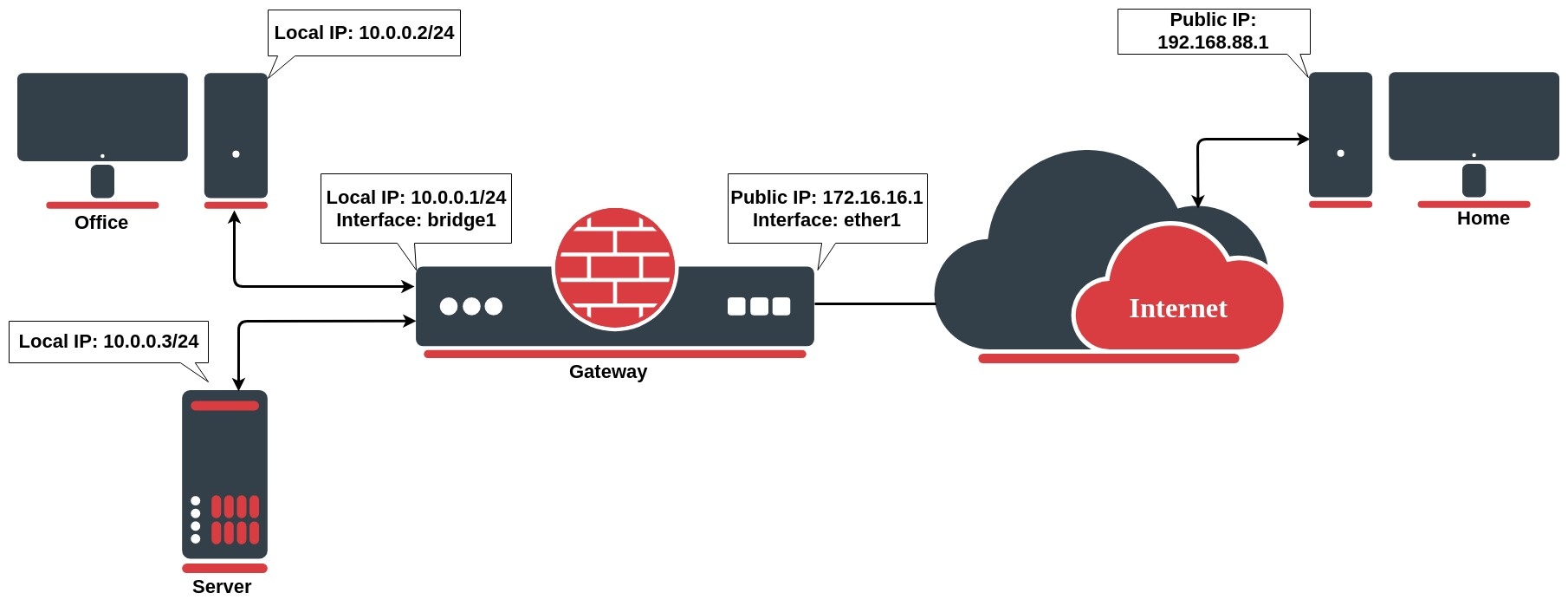 Image Added
Image Added
Network address translation works by modifying network address information in the packet's IP header. Let`s take a look at the common setup where a network administrator wants to access an office server from the internet.
We want to allow connections from the internet to the office server whose local IP is 10.0.0.3
...
. In this case, we have to configure a destination address translation rule on the office gateway router:
| Code Block |
|---|
|
/ip firewall nat add chain=dstnat action=dst-nat dst-address=172.16.16.1 dst-port=22 to-addresses=10.0.0.3 protocol=tcp |
The rule above translates: when an incoming connection requests TCP port 22 with destination address
| Tip |
|---|
To allow access only from the PC at home, we can improve our dst-nat rule with "src-address=192.168.88.1" which is a Home`s PC public (this examples) IP address. It is also considered to be more secure! |
Source NAT
...
172.16.16.1,
...
use the dst-nat action and depart packets to the device with local IP address 10.0.0.3 and port 22.
| Tip |
|---|
To allow access only from the PC at home, we can improve our dst-nat rule with "src-address=192.168.88.1" which is a Home`s PC public (this example) IP address. It is also considered to be more secure! |
Source NAT
If you want to hide your local devices behind your public IP address received from the ISP, you should configure the source network address translation (masquerading) feature of the MikroTik router.
Let`s assume you want to hide both the office computer and server behind the public
| Code Block |
|---|
|
/ip firewall nat add chain=srcnat src-address=10.0.0.0/24 action=src-nat to-addresses=172.16.16.1 out-interface=WAN |
Now your ISP will see all the requests coming with IP 172.16.16.1 and they will not see your LAN network IP addresses.
Masquerade
, the rule will look like the following one:
| Code Block |
|---|
|
/ip firewall nat add chain=srcnat src-address=10.0.0.0/24 action=src-nat to-addresses=172.16.16.1 out-interface=WAN |
Now your ISP will see all the requests coming with IP 172.16.16.1 and they will not see your LAN network IP addresses.
Masquerade
Firewall NAT action=Firewall NAT action=masqueradeis a unique subversion of action=srcnat, it was designed for specific use in situations when public IP can randomly change, for example, DHCP server change changes assigned IP or PPPoE tunnel after disconnect gets a different IP, in short - when public IP is dynamic.
| Code Block |
|---|
|
/ip firewall nat add chain=srcnat src-address=10.0.0.0/24 action=masquarademasquerade out-interface=WAN |
Every time when interface disconnects and/or its IP address changes, the router will clear all masqueraded connection tracking entries related to the interface, this way improving system recovery time after public IP change. If srcnat is used instead of masquerade, connection tracking entries remain and connections can simply resume after a link failure.
...
- on disconnect, all related connection tracking entries are purged;
- next packet from every purged (previously masqueraded) connection will come into the firewall as new, and, if a primary interface is not back, a packet will be routed out via an alternative route (if you have any) thus creating a new masqueraded connection;
- the primary link comes back, routing is restored over the primary link, so packets that belong to existing connections are sent over the primary interface without being masqueraded, that way leaking local IPs to a public network.
...
To overcome these limitations RouterOS includes a number of so-called NAT helpers, that enable NAT traversal for various protocols. When action=srcnat is used instead, connection tracking entries remain and connections can simply resume.
| Tip |
|---|
Though Source NAT and masquerading perform the same fundamental function: mapping one address space into another one, the details differ slightly. Most noticeably, masquerading chooses the source IP address for the outbound packet from the IP bound to the interface through which the packet will exit. |
Hairpin NAT
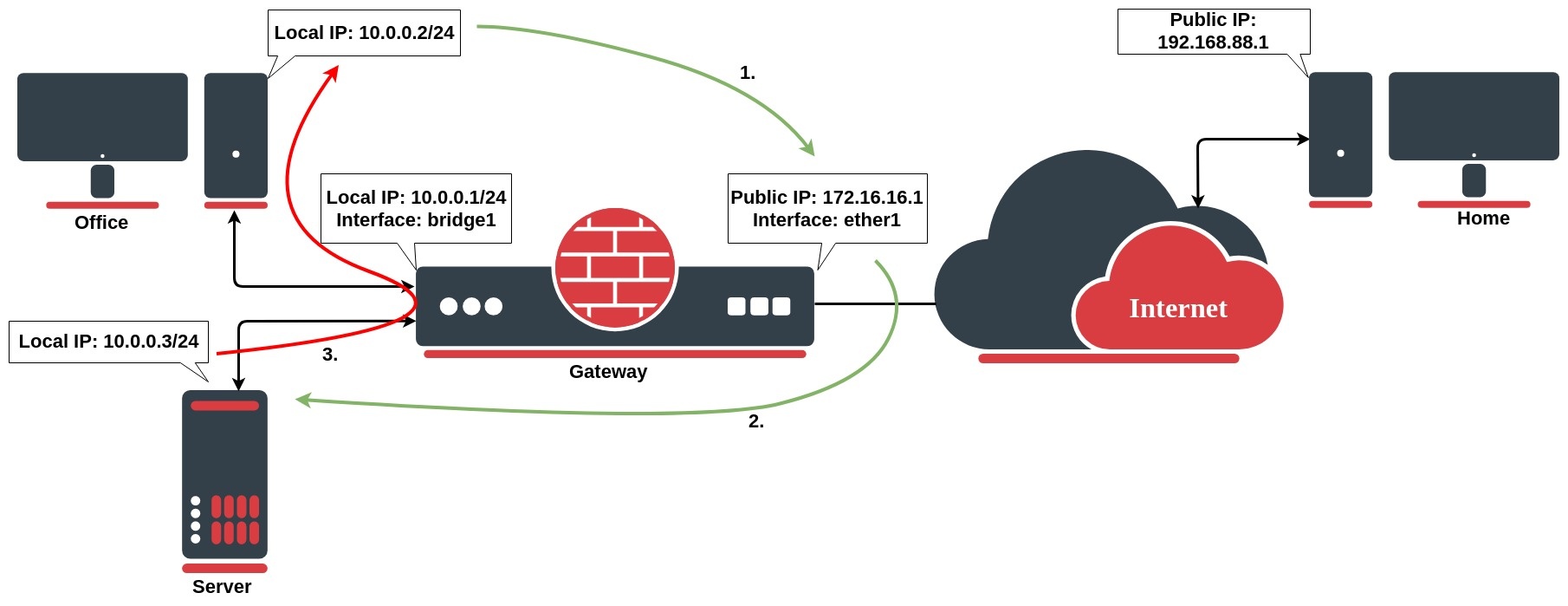
Hairpin network address translation (NAT Loopback) is where the device on the LAN is able to access another machine on the LAN via the public IP address of the gateway router.
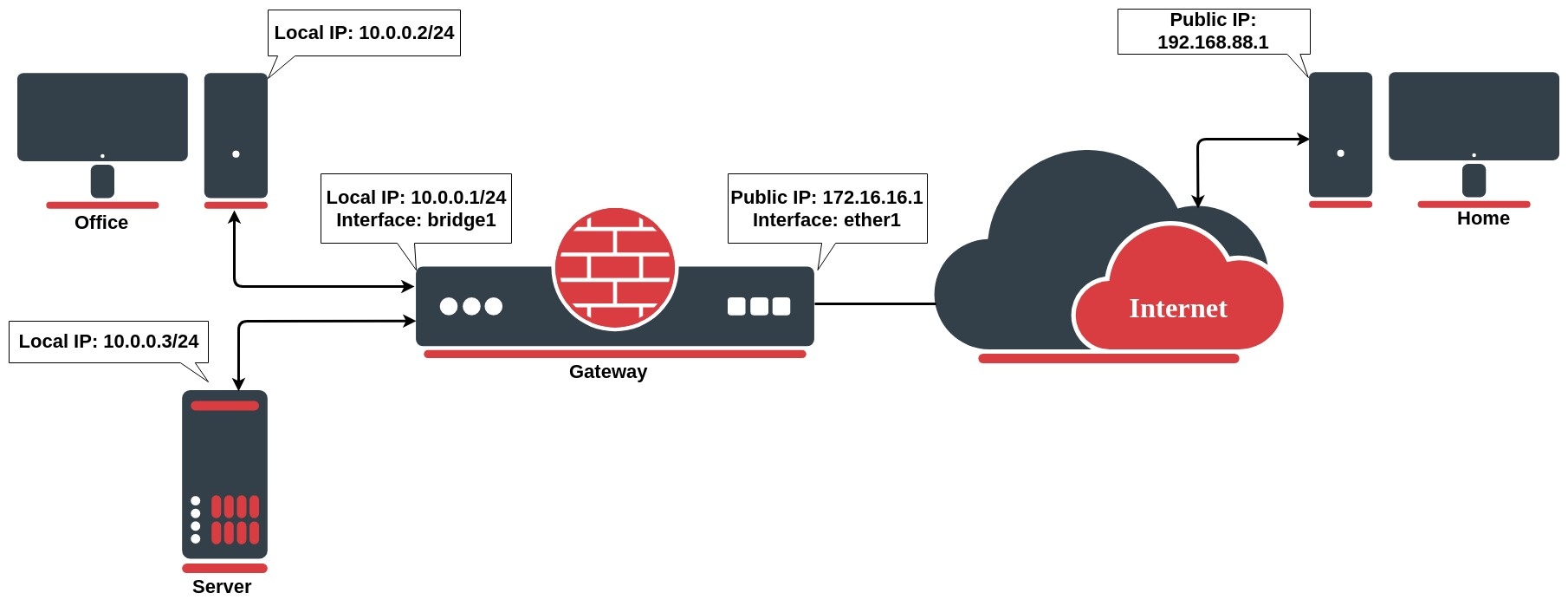 Image Removed
Image Removed
CGNAT (NAT444)
 Image Added
Image Added
To combat IPv4 address exhaustion, a new RFC 6598 was deployed. The idea is to use shared 100.64.0.0/10 address space inside the carrier's network and perform NAT on the carrier's edge router to a single public IP or public IP range.
Because of the nature of such a setup, it is also called NAT444, as opposed to a NAT44 network for a 'normal' NAT environment, three different IPv4 address spaces are involved.
CGNAT configuration on RouterOS does not differ from any other regular source NAT configurationIn the following example gateway router consist of dst-nat configuration rule:
| Code Block |
|---|
|
/ip firewall nat
add chain=dstnatsrc-nat action=dst-natsrcnat dstsrc-address=172100.1664.160.1 dst-port=443 0/10 to-addressesaddress=102.02.02.32 toout-ports=443 protocol=tcp |
When a customer from the PC at home establishes a connection to the webserver, the router performs NAT as configured:
- the client sends a packet with a source IP address of 192.168.88.1 to a destination IP address of 172.16.16.1 on port 443 to request some web resource;
- the router destination NAT`s the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 192.168.88.1;
- the server replies to the client's request and the reply packet have a source IP address of 10.0.0.3 and a destination IP address of 192.168.88.1.
- the router determines that the packet is part of a previous connection and undoes the destination NAT, and puts the original destination IP address into the source IP address field. The destination IP address is 192.168.88.1, and the source IP address is 172.16.16.1;
- The client receives the reply packet it expects, and the connection is established;
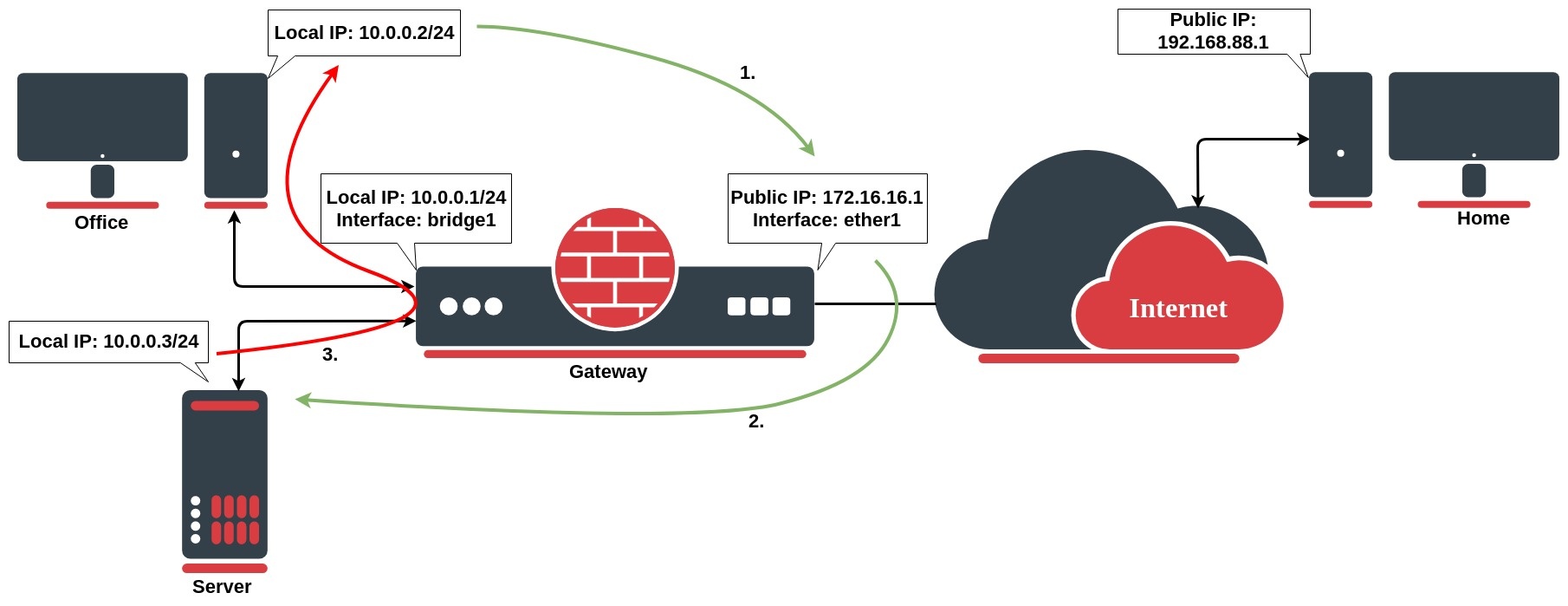 Image Removed
Image Removed
The issue occurs, when a client on the same internal network as the webserver requests a connection to the web server's public IP address, the connection breaks:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resource;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 10.0.0.2;
- the server replies to the client's request. However, the source IP address of the request is on the same subnet as the webserver. The web server does not send the reply back to the router but sends it back directly to 10.0.0.2 with a source IP address in the reply of 10.0.0.3;
- The client receives the reply packet, but it discards it because it expects a packet back from 172.16.16.1, and not from 10.0.0.3;
To resolve this issue, we will configure the src-nat rule as follows:
| Code Block |
|---|
|
/ip firewall nat
add action=masquerade chain=srcnat dst-address=10.0.0.3 out-interface=LAN protocol=tcp src-address=10.0.0.0/24 |
After configured rule above:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resource;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. It also source NATs the packet and replaces the source IP address in the packet with the IP address on its LAN interface. The destination IP address is 10.0.0.3, and the source IP address is 10.0.0.1;
- the web server replies to the request and sends the reply with a source IP address of 10.0.0.3 back to the router's LAN interface IP address of 10.0.0.1;
- the router determines that the packet is part of a previous connection and undoes both the source and destination NAT, and puts the original destination IP address of 1.1.1.1 into the source IP address field, and the original source IP address of 172.16.16.1 into the destination IP address field
Properties
Where:
- 2.2.2.2 - public IP address,
- public_if - interface on provider's edge router connected to the internet
The advantage of NAT444 is obvious, fewer public IPv4 addresses are used. But this technique comes with major drawbacks:
- The service provider router performing CGNAT needs to maintain a state table for all the address translations: this requires a lot of memory and CPU resources.
- Console gaming problems. Some games fail when two subscribers using the same outside public IPv4 address try to connect to each other.
- Tracking users for legal reasons means extra logging, as multiple households go behind one public address.
- Anything requiring incoming connections is broken. While this already was the case with regular NAT, end-users could usually still set up port forwarding on their NAT router. CGNAT makes this impossible. This means no web servers can be hosted here, and IP Phones cannot receive incoming calls by default either.
- Some web servers only allow a maximum number of connections from the same public IP address, as a means to counter DoS attacks like SYN floods. Using CGNAT this limit is reached more often and some services may be of poor quality.
- 6to4 requires globally reachable addresses and will not work in networks that employ addresses with a limited topological span.
Packets with Shared Address Space source or destination addresses MUST NOT be forwarded across Service Provider boundaries. Service Providers MUST filter such packets on ingress links. In RouterOS this can be easily done with firewall filters on edge routers:
| Code Block |
|---|
|
/ip firewall filter
add chain=input src-address=100.64.0.0/10 action=drop in-interface=<public_if>
add chain=output dst-address=100.64.0.0/10 action=drop out-interface=<public_if>
add chain=forward src-address=100.64.0.0/10 action=drop in-interface=<public_if>
add chain=forward src-address=100.64.0.0/10 action=drop out-interface=<public_if>
add chain=forward dst-address=100.64.0.0/10 action=drop out-interface=<public_if> |
Service providers may be required to log of MAPed addresses, in a large CGN deployed network which may be a problem. Fortunately, RFC 7422 suggests a way to manage CGN translations in such a way as to significantly reduce the amount of logging required while providing traceability for abuse response.
RFC states that instead of logging each connection, CGNs could deterministically map customer private addresses (received on the customer-facing interface of the CGN, a.k.a., internal side) to public addresses extended with port ranges.
That means that separate NAT rules have to be added to achieve individual mappings such as the ones seen in the below example:
| Inside IP | Outside IP/Port range |
| 100.64.0.1 | 2.2.2.2:5000-5199 |
| 100.64.0.2 | 2.2.2.2:5200-5399 |
| 100.64.0.3 | 2.2.2.2:5400-5599 |
| 100.64.0.4 | 2.2.2.2:5600-5799 |
| 100.64.0.5 | 2.2.2.2:5800-5999 |
Instead of writing the rules by hand, it is suggested to use a script instead. The following example could be adapted to any requirements of your setup.
| Code Block |
|---|
|
{
######## Adjustable values #########
:local StartingAddress 100.64.0.1
:local ClientCount 5
:local AddressesPerClient 2
:local PublicAddress 2.2.2.2
:local StartingPort 5000
:local PortsPerAddress 200
####################################
# All client chain jump
/ip firewall nat add chain=srcnat action=jump jump-target=clients \
src-address="$StartingAddress-$($StartingAddress + ($ClientCount * $AddressesPerClient) - 1)"
:local currentPort $StartingPort
:for c from=1 to=$ClientCount do={
# Specific client chain jumps
:if ($AddressesPerClient > 1) do={
/ip firewall nat add chain=clients action=jump jump-target="client-$c" \
src-address="$($StartingAddress + ($AddressesPerClient * ($c - 1)))-$($StartingAddress + ($AddressesPerClient * $c -1))"
} else={
/ip firewall nat add chain=clients action=jump jump-target="client-$c" \
src-address="$($StartingAddress + ($AddressesPerClient * ($c - 1)))"
}
# Translation rules
:for a from=1 to=$AddressesPerClient do={
/ip firewall nat add chain="client-$c" action=src-nat protocol=tcp \
src-address="$($StartingAddress + (($c -1) * $AddressesPerClient) + $a - 1)" to-address=$PublicAddress to-ports="$currentPort-$($currentPort + $PortsPerAddress - 1)"
/ip firewall nat add chain="client-$c" action=src-nat protocol=udp \
src-address="$($StartingAddress + (($c -1) * $AddressesPerClient) + $a - 1)" to-address=$PublicAddress to-ports="$currentPort-$($currentPort + $PortsPerAddress - 1)"
:set currentPort ($currentPort + $PortsPerAddress)
}
}
} |
The six local values can be adjusted and the script can be either simply pasted in the terminal or it can be stored in the system script section, in case the configuration needs to be regenerated later.
After execution, you should get a set of rules:
| Code Block |
|---|
|
[admin@MikroTik] > ip firewall nat print
Flags: X - disabled, I - invalid; D - dynamic
0 chain=srcnat action=jump jump-target=clients
src-address=100.64.0.1-100.64.0.10
1 chain=clients action=jump jump-target=client-1
src-address=100.64.0.1-100.64.0.2
2 chain=client-1 action=src-nat to-addresses=2.2.2.2 to-ports=5000-5199
protocol=tcp src-address=100.64.0.1
3 chain=client-1 action=src-nat to-addresses=2.2.2.2 to-ports=5000-5199
protocol=udp src-address=100.64.0.1
4 chain=client-1 action=src-nat to-addresses=2.2.2.2 to-ports=5200-5399
protocol=tcp src-address=100.64.0.2
5 chain=client-1 action=src-nat to-addresses=2.2.2.2 to-ports=5200-5399
protocol=udp src-address=100.64.0.2
6 chain=clients action=jump jump-target=client-2
src-address=100.64.0.3-100.64.0.4
7 chain=client-2 action=src-nat to-addresses=2.2.2.2 to-ports=5400-5599
protocol=tcp src-address=100.64.0.3
8 chain=client-2 action=src-nat to-addresses=2.2.2.2 to-ports=5400-5599
protocol=udp src-address=100.64.0.3
9 chain=client-2 action=src-nat to-addresses=2.2.2.2 to-ports=5600-5799
protocol=tcp src-address=100.64.0.4
10 chain=client-2 action=src-nat to-addresses=2.2.2.2 to-ports=5600-5799
protocol=udp src-address=100.64.0.4
11 chain=clients action=jump jump-target=client-3
src-address=100.64.0.5-100.64.0.6
12 chain=client-3 action=src-nat to-addresses=2.2.2.2 to-ports=5800-5999
protocol=tcp src-address=100.64.0.5
13 chain=client-3 action=src-nat to-addresses=2.2.2.2 to-ports=5800-5999
protocol=udp src-address=100.64.0.5
14 chain=client-3 action=src-nat to-addresses=2.2.2.2 to-ports=6000-6199
protocol=tcp src-address=100.64.0.6
15 chain=client-3 action=src-nat to-addresses=2.2.2.2 to-ports=6000-6199
protocol=udp src-address=100.64.0.6
[...] |
Hairpin NAT
Hairpin network address translation (NAT Loopback) is where the device on the LAN can access another machine on the LAN via the public IP address of the gateway router.
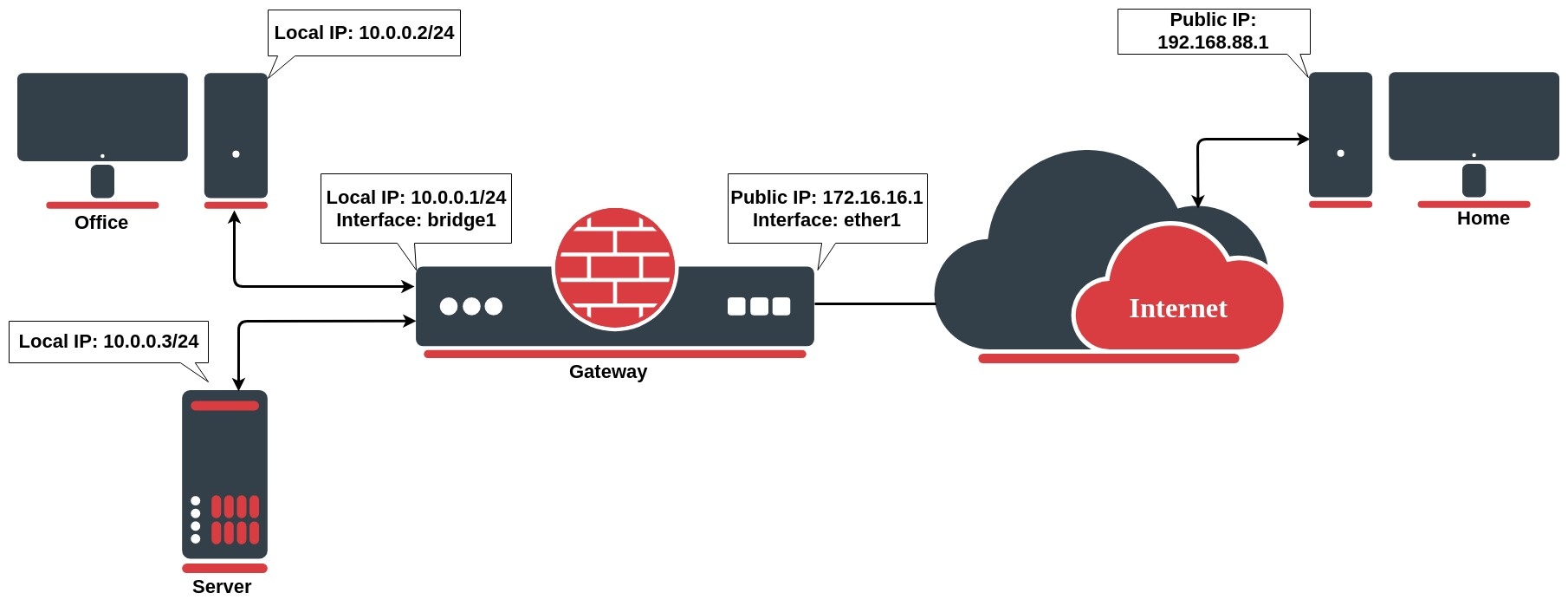 Image Added
Image Added
In the above example, the gateway router has the following dst-nat configuration rule:
| Code Block |
|---|
|
/ip firewall nat add chain=dstnat action=dst-nat dst-address=172.16.16.1 dst-port=443 to-addresses=10.0.0.3 to-ports=443 protocol=tcp |
When a user from the PC at home establishes a connection to the web server, the router performs DST NAT as configured:
- the client sends a packet with a source IP address of 192.168.88.1 to a destination IP address of 172.16.16.1 on port 443 to request some web resources;
- the router destination NAT`s the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 192.168.88.1;
- the server replies to the client's request and the reply packet has a source IP address of 10.0.0.3 and a destination IP address of 192.168.88.1.
- the router determines that the packet is part of a previous connection and undoes the destination NAT, and puts the original destination IP address into the source IP address field. The destination IP address is 192.168.88.1, and the source IP address is 172.16.16.1;
- The client receives the reply packet it expects, and the connection is established;
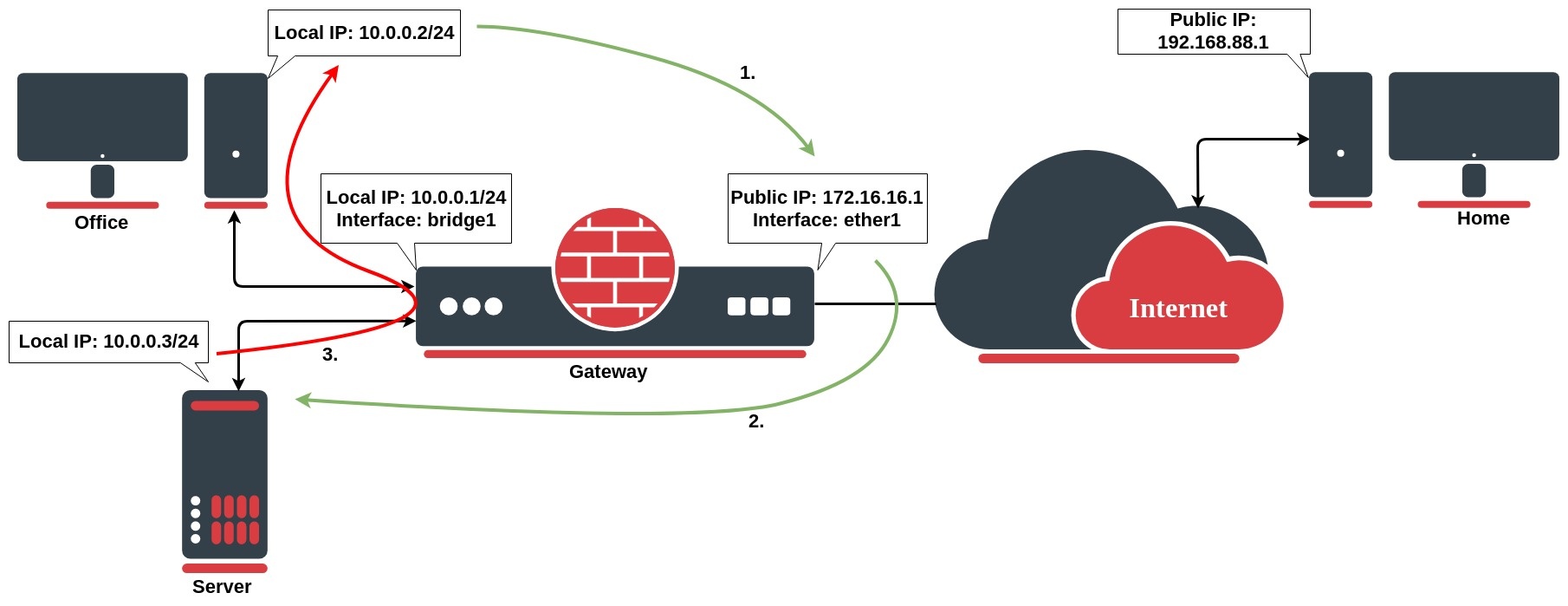 Image Added
Image Added
But, there will be a problem, when a client on the same network as the web server requests a connection to the web server's public IP address:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resources;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. The source IP address stays the same: 10.0.0.2;
- the server replies to the client's request. However, the source IP address of the request is on the same subnet as the web server. The web server does not send the reply back to the router but sends it back directly to 10.0.0.2 with a source IP address in the reply of 10.0.0.3;
- The client receives the reply packet, but it discards it because it expects a packet back from 172.16.16.1, and not from 10.0.0.3;
To resolve this issue, we will configure a new src-nat rule (the hairpin NAT rule) as follows:
| Code Block |
|---|
|
/ip firewall nat
add action=masquerade chain=srcnat dst-address=10.0.0.3 out-interface=LAN protocol=tcp src-address=10.0.0.0/24 |
After configuring the rule above:
- the client sends a packet with a source IP address of 10.0.0.2 to a destination IP address of 172.16.16.1 on port 443 to request some web resources;
- the router destination NATs the packet to 10.0.0.3 and replaces the destination IP address in the packet accordingly. It also source NATs the packet and replaces the source IP address in the packet with the IP address on its LAN interface. The destination IP address is 10.0.0.3, and the source IP address is 10.0.0.1;
- the web server replies to the request and sends the reply with a source IP address of 10.0.0.3 back to the router's LAN interface IP address of 10.0.0.1;
- the router determines that the packet is part of a previous connection and undoes both the source and destination NAT, and puts the original destination IP address of 10.0.0.3 into the source IP address field, and the original source IP address of 172.16.16.1 into the destination IP address field
Endpoint-Independent NAT
Endpoint-independent NAT creates mapping in the source NAT and uses the same mapping for all subsequent packets with the same source IP and port. This mapping is created with the following rule:
| Code Block |
|---|
|
/ip firewall nat
add action=endpoint-independent-nat chain=srcnat out-interface=WAN protocol=udp |
This mapping allows running source-independent filtering, which allows forwarding packets from any source from WAN to mapped internal IP and port. The following rule enables filtering:
| Code Block |
|---|
|
/ip firewall nat
add action=endpoint-independent-nat chain=dstnat in-interface=WAN protocol=udp |
| Note |
|---|
Endpoint-independent NAT works only with UDP protocol. |
Additionally, endpoint-independent-nat can take a few other parameters:
randomize-port - randomize to which public port connections will be mapped.
More info https://www.ietf.org/rfc/rfc5128.txt section 2.2.3 and 2.2.5
IPv4
Properties
| Property | Description |
|---|
| action (action name; Default: accept) | Action to take if a packet is matched by the rule:accept - accept the packet. A packet is not passed to the next NAT rule.add-dst-to-address-list - add the destination address to the address list specified by address-list parameteradd-src-to-address-list - add the source address to the address list specified by address-list parameterdst-nat - replaces the destination address and/or port of an IP packet with values specified by to-addresses and to-ports parametersjump - jump to the user-defined chain specified by the value of jump-target parameterlog - add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port and length of the packet. After a packet is matched it is passed to the next rule in the list, similar as passthroughmasquerade - replaces the source port of an IP packet with one specified by to-ports parameter and replace the source address of an IP packet to the IP determined by the routing facility. netmap - creates a static 1:1 mapping of one set of IP addresses to another one. Often used to distribute public IP addresses to hosts on private networkspassthrough - if a packet is matched by the rule, increase the counter and go to the next rule (useful for statistics).redirect - replaces the destination port of an IP packet with one specified by to-ports parameter and destination address to one of the router's local addressesreturn - passes control back to the chain from where the jump took placesame - gives a particular client the same source/destination IP address from a supplied range for each connection. This is most frequently used for services that expect the same client address for multiple connections from the same clientsrc-nat - replaces the source address of an IP packet with values specified by to-addresses and to-ports parametersendpoint-independent-nat - uses endpoint-independent mapping and filtering. Works only with UDP protocol.
|
| address-list (string; Default: ) | Name of the address list to be used. Applicable if action is add-dst-to-address-list or add-src-to-address-list |
| address-list-timeout (none-dynamic | none-static | time; Default: none-dynamic) | Time interval after which the address will be removed from the address list specified by address-list parameter. Used in conjunction with add-dst-to-address-list or add-src-to-address-list actions
- Value of none-dynamic (
00:00:00) will leave the address in the address list till the reboot - Value of none-static will leave the address in the address list forever and will be included in the configuration export/backup
|
| chain (name; Default: ) | Specifies to which chain rule will be added. If the input does not match the name of an already defined chain, a new chain will be created |
| comment (string; Default: ) | Descriptive comment for the rule |
| connection-bytes (integer-integer; Default: ) | Matches packet only if a given amount of bytes has been transferred through the particular connection. 0 - means infinity, for example connection-bytes=2000000-0 means that the rule matches if more than 2MB has been transferred through the relevant connection |
| connection-limit (integer,netmask; Default: ) | Matches connections per address or address block after a given value is reached |
| connection-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular connection mark. If a no-mark is set, the rule will match any unmarked connection |
| connection-rate (Integer 0..4294967295; Default: ) | Connection Rate is a firewall matcher that allows capturing traffic based on the present speed of the connection |
| connection-type (ftp | h323 | irc | pptp | quake3 | sip | tftp; Default: ) | Matches packets from related connections based on information from their connection tracking helpers. A relevant connection helper must be enabled under /ip firewall service-port |
| content (string; Default: ) | Match packets that contain specified text |
| dscp (integer: 0..63; Default: ) | Matches DSCP IP header field. |
| dst-address (IP/netmask | IP range; Default: ) | Matches packets whose destination is equal to a specified IP or falls into a specified IP range. |
| dst-address-list (name; Default: ) | Matches the destination address of a packet against a user-defined address list |
| dst-address-type (unicast | local | broadcast | multicast; Default: ) | Matches destination address type:unicast - IP address used for point-to-point transmissionlocal - if dst-address is assigned to one of the router's interfacesbroadcast - packet is sent to all devices in a subnetmulticast - packet is forwarded to a defined group of devices
|
| dst-limit (integer[/time],integer,dst-address | dst-port | src-address[/time]; Default: ) | Matches packets until a given PPS limit is exceeded. As opposed to the limit matcher, every destination IP address/destination port has its own limit. Parameters are written in the following format: count[/time],burst,mode[/expire].- count - maximum average packet rate measured in packets per
time interval - time - specifies the time interval in which the packet rate is measured (optional)
- burst - number of packets that are not counted by packet rate
- mode - the classifier for packet rate limiting
- expire - specifies interval after which recorded IP address /port will be deleted (optional)
|
| dst-port (integer[-integer]: 0..65535; Default: ) | List of destination port numbers or port number ranges in format Range[,Port], for example, dst-port=123-345,456-678 |
| fragment (yes|no; Default: ) | Matches fragmented packets. The first (starting) fragment does not count. If connection tracking is enabled there will be no fragments as the system automatically assembles every packet |
| hotspot (auth | from-client | http | local-dst | to-client; Default: ) | Matches packets received from HotSpot clients against various HotSpot matchers.auth - matches authenticated HotSpot client packetsfrom-client - matches packets that are coming from the HotSpot clienthttp - matches HTTP requests sent to the HotSpot serverlocal-dst - matches packets that are destined to the HotSpot serverto-client - matches packets that are sent to the HotSpot client
|
| icmp-options (integer:integer; Default: ) | Matches ICMP type: code fields |
| in-bridge-port (name; Default: ) | Actual interface the packet has entered the router if the incoming interface is a bridge |
| in-interface (name; Default: ) | Interface the packet has entered the router |
| ingress-priority (integer: 0..63; Default: ) | Matches ingress the priority of the packet. Priority may be derived from VLAN, WMM or MPLS EXP bit. |
| ipsec-policy (in | out, ipsec | none; Default: ) | Matches the policy used by IPSec. Value is written in the following format: direction, policy. The direction is Used to select whether to match the policy used for decapsulation or the policy that will be used for encapsulation.in - valid in the PREROUTING, INPUT, and FORWARD chainsout - valid in the POSTROUTING, OUTPUT, and FORWARD chains
ipsec - matches if the packet is subject to IPsec processing;none - matches packet that is not subject to IPsec processing (for example, IPSec transport packet).
For example, if a router receives an IPsec encapsulated Gre packet, then the rule ipsec-policy=in,ipsec will match the Gre packet, but the rule ipsec-policy=in,none will match the ESP packet. |
| ipv4-options (any | loose-source-routing | no-record-route | no-router-alert | no-source-routing | no-timestamp | none | record-route | router-alert | strict-source-routing | timestamp; Default: ) | Matches IPv4 header options.any - match packet with at least one of the ipv4 optionsloose-source-routing - match packets with a loose source routing option. This option is used to route the internet datagram based on information supplied by the sourceno-record-route - match packets with no record route option. This option is used to route the internet datagram based on information supplied by the sourceno-router-alert - match packets with no router alter optionno-source-routing - match packets with no source routing optionno-timestamp - match packets with no timestamp optionrecord-route - match packets with record route optionrouter-alert - match packets with router alter optionstrict-source-routing - match packets with a strict source routing optiontimestamp - match packets with a timestamp
|
| jump-target (name; Default: ) | Name of the target chain to jump to. Applicable only if action=jump |
| layer7-protocol (name; Default: ) | Layer7 filter name defined in layer7 protocol menu. |
| limit (integer,time,integer; Default: ) | Matches packets until a given PPS limit is exceeded. Parameters are written in the following format: count[/time],burst.- count - maximum average packet rate measured in packets per
time interval - time - specifies the time interval in which the packet rate is measured (optional, 1s will be used if not specified)
- burst - number of packets that are not counted by packet rate
|
| log (yes | no; Default: no) | Add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port, and length of the packet. |
| log-prefix (string; Default: ) | Adds specified text at the beginning of every log message. Applicable if action=log or log=yes configured. |
| out-bridge-port (name; Default: ) | Actual interface the packet is leaving the router if the outgoing interface is a bridge |
| out-interface (; Default: ) | Interface the packet is leaving the router |
| packet-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular packet mark. If no-mark is set, the rule will match any unmarked packet |
| packet-size (integer[-integer]:0..65535; Default: ) | Matches packets of specified size or size range in bytes |
| per-connection-classifier (ValuesToHash:Denominator/Remainder; Default: ) | PCC matcher allows dividing traffic into equal streams with the ability to keep packets with a specific set of options in one particular stream |
| port (integer[-integer]: 0..65535; Default: ) | Matches if any (source or destination) port matches the specified list of ports or port ranges. Applicable only if protocol is TCP or UDP |
| protocol (name or protocol ID; Default: tcp) | Matches particular IP protocol specified by protocol name or number |
| psd (integer,time,integer,integer; Default: ) | Attempts to detect TCP and UDP scans. Parameters are in the following format WeightThreshold, DelayThreshold, LowPortWeight, HighPortWeight- WeightThreshold - total weight of the latest TCP/UDP packets with different destination ports coming from the same host to be treated as port scan sequence
- DelayThreshold - delay for the packets with different destination ports coming from the same host to be treated as possible port scan subsequence
- LowPortWeight - the weight of the packets with privileged (<1024) destination port
- HighPortWeight - the weight of the packet with a non-privileged destination port
|
| random (integer: 1..99; Default: ) | Matches packets randomly with a given probability |
| routing-mark (string; Default: ) | Matches packets marked by mangle facility with particular routing mark |
| same-not-by-dst (yes | no; Default: ) | Specifies whether to take into account or not the destination IP address when selecting a new source IP address. Applicable if action=same |
| src-address (Ip/Netmaks, Ip range; Default: ) | Matches packets whose source is equal to a specified IP or falls into a specified IP range. |
| src-address-list (name; Default: ) | Matches the source address of a packet against a user-defined address list |
| src-address-type (unicast | local | broadcast | multicast; Default: ) | Matches source address type: unicast - IP address used for point-to-point transmissionlocal - if an address is assigned to one of the router's interfacesbroadcast - packet is sent to all devices in a subnetmulticast - packet is forwarded to a defined group of devices
|
| src-port (integer[-integer]: 0..65535; Default: ) | List of source ports and ranges of source ports. Applicable only if a protocol is TCP or UDP. |
| src-mac-address (MAC address; Default: ) | Matches the source MAC address of the packet |
| tcp-mss (integer[-integer]: 0..65535; Default: ) | Matches the TCP MSS value of an IP packet |
| time (time-time,sat | fri | thu | wed | tue | mon | sun; Default: ) | Allows to create a filter based on the packets' arrival time and date or, for locally generated packets, departure time and date |
| to-addresses (IP address[-IP address]; Default: 0.0.0.0) | Replace the original address with the specified one. Applicable if action is dst-nat, netmap, same, src-nat |
| to-ports (integer[-integer]: 0..65535; Default: ) | Replace the original port with the specified one. Applicable if action is dst-nat, redirect, masquerade, netmap, same, src-nat |
| ttl (integer: 0..255; Default: ) | Matches packet's TTL value |
Stats
| Property | Description |
|---|
| bytes (integer) | The total amount of bytes matched by the rule |
| packets (integer) | The total amount of packets matched by the rule |
To show additional read-only properties:
| Code Block |
|---|
|
[admin@MikroTik] > ip firewall nat print stats all
Flags: X - disabled, I - invalid, D - dynamic
# CHAIN ACTION BYTES PACKETS
0 srcnat masquerade 265 659 987 |
IPv6
NAT66 is supported since RouterOS v7.1.
| Code Block |
|---|
|
ipv6/firewall/nat/ |
Properties
| Property | Description |
|---|
| action (action name; Default: accept) | Action to take if a packet is matched by the rule:accept - accept the packet. A packet is not passed to the next NAT rule.
|
| Property | Description |
|---|
action (action name; Default: accept) | Action to take if a packet is matched by the rule:accept - accept the packet. A packet is not passed to the next NAT rule.add-dst-to-address-list - add the destination address to the address list specified by address-list parameteradd-src-to-address-list - add the source address to the address list specified by address-list parameterdst-nat - replaces the destination address
|
-list- and/or port of an IP packet with values specified by
to-addresses and to-ports parameters jump - jump to the user-defined chain specified by the value of jump-target parameterlog - add a message to the system log containing the following data: in-interface, out-interface, src-
|
to-address-list - add source address to address list specified by address-list parameterdst-nat - replaces destination address and/or port - mac, protocol, src-ip:port->dst-ip:port and length of the packet. After a packet is matched it is passed to the next rule in the list, similar as
passthrough masquerade - replaces the source port of an IP packet with one specified by to-ports parameter and replace the source address of an IP packet to
|
values specified by to-addresses and to-ports parametersjump - jump to the user-defined chain specified by the value of jump-target parameterlog - add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port and length of the packet. After a packet is matched it is passed to the next rule in the list, similar as passthroughmasquerade - replaces source port of an IP packet to one specified by to-ports parameter and replace the source address of an IP packet to IP determined by routing facility. netmap - creates a static 1:1 mapping of one set of IP addresses to another one. Often used to distribute public IP addresses to hosts on private networkspassthrough - if a packet is matched by the rule, increase counter and go to next rule (useful for statistics).redirect - replaces destination port of an IP packet to one specified by to-ports parameter and destination address to one of the router's local addressesreturn - passes control back to the chain from where the jump took placesame - gives a particular client the same source/destination IP address from a supplied range for each connection. This is most frequently used for services that expect the same client address for multiple connections from the same clientsrc-nat - replaces source address of an IP packet to values specified by to-addresses and to-ports parameters| address-list (string; Default: ) | Name of the address list to be used. Applicable if action is add-dst-to-address-list or add-src-to-address-list |
| address-list-timeout (none-dynamic | none-static | time; Default: none-dynamic) | Time interval after which the address will be removed from the address list specified by address-list parameter. Used in conjunction with add-dst-to-address-list or add-src-to-address-list actions
- Value of none-dynamic (
00:00:00) will leave the address in the address list till reboot - Value of none-static will leave the address in the address list forever and will be included in configuration export/backup
|
| chain (name; Default: ) | Specifies to which chain rule will be added. If the input does not match the name of an already defined chain, a new chain will be created |
| comment (string; Default: ) | Descriptive comment for the rule |
| connection-bytes (integer-integer; Default: ) | Matches packets only if a given amount of bytes has been transferred through the particular connection. 0 - means infinity, for example connection-bytes=2000000-0 means that the rule matches if more than 2MB has been transferred through the relevant connection |
| connection-limit (integer,netmask; Default: ) | Matches connections per address or address block after a given value is reached |
| connection-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular connection mark. If no-mark is set, the rule will match any unmarked connection |
| connection-rate (Integer 0..4294967295; Default: ) | Connection Rate is a firewall matcher that allows capturing traffic based on the present speed of the connection |
| connection-type (ftp | h323 | irc | pptp | quake3 | sip | tftp; Default: ) | Matches packets from related connections based on information from their connection tracking helpers. A relevant connection helper must be enabled under /ip firewall service-port |
| content (string; Default: ) | Match packets that contain specified text |
| dscp (integer: 0..63; Default: ) | Matches DSCP IP header field. |
| dst-address (IP/netmask | IP range; Default: ) | Matches packets which destination is equal to specified IP or falls into specified IP range. |
| dst-address-list (name; Default: ) | Matches destination address of a packet against user-defined address list |
| dst-address-type (unicast | local | broadcast | multicast; Default: ) | Matches destination address type:- unicast - IP address used for point to point transmission
- local - if dst-address is assigned to one of the router's interfaces
- broadcast - packet is sent to all devices in a subnet
- multicast - packet is forwarded to a defined group of devices
|
| dst-limit (integer[/time],integer,dst-address | dst-port | src-address[/time]; Default: ) | Matches packets until a given pps limit is exceeded. As opposed to the limit matcher, every destination IP address/destination port has its own limit. Parameters are written in the following format: count[/time],burst,mode[/expire].- count - maximum average packet rate measured in packets per
time interval - time - specifies the time interval in which the packet rate is measured (optional)
- burst - number of packets that are not counted by packet rate
- mode - the classifier for packet rate limiting
- expire - specifies interval after which recored ip address /port will be deleted (optional)
|
| dst-port (integer[-integer]: 0..65535; Default: ) | List of destination port numbers or port number ranges |
| fragment (yes|no; Default: ) | Matches fragmented packets. The first (starting) fragment does not count. If connection tracking is enabled there will be no fragments as the system automatically assembles every packet |
hotspot (auth | from-client | http | local-dst | to-client; Default: ) | - IP determined by the routing facility.
netmap - creates a static 1:1 mapping of one set of IP addresses to another one. Often used to distribute public IP addresses to hosts on private networkspassthrough - if a packet is matched by the rule, increase the counter and go to the next rule (useful for statistics).redirect - replaces the destination port of an IP packet with one specified by to-ports parameter and destination address to one of the router's local addressesreturn - passes control back to the chain from where the jump took placesrc-nat - replaces the source address of an IP packet with values specified by to-addresses and to-ports parameters
|
| address-list (string; Default: ) | Name of the address list to be used. Applicable if action is add-dst-to-address-list or add-src-to-address-list |
| address-list-timeout (none-dynamic | none-static | time; Default: none-dynamic) | Time interval after which the address will be removed from the address list specified by address-list parameter. Used in conjunction with add-dst-to-address-list or add-src-to-address-list actions
- Value of none-dynamic (
00:00:00) will leave the address in the address list till reboot - Value of none-static will leave the address in the address list forever and will be included in the configuration export/backup
|
| chain (name; Default: ) | Specifies to which chain rule will be added. If the input does not match the name of an already defined chain, a new chain will be created |
| comment (string; Default: ) | Descriptive comment for the rule |
| connection-bytes (integer-integer; Default: ) | Matches packets only if a given amount of bytes has been transferred through the particular connection. 0 - means infinity, for example connection-bytes=2000000-0 means that the rule matches if more than 2MB has been transferred through the relevant connection |
| connection-limit (integer,netmask; Default: ) | Matches connections per address or address block after a given value is reached |
| connection-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular connection mark. If no-mark is set, the rule will match any unmarked connection |
| connection-rate (Integer 0..4294967295; Default: ) | Connection Rate is a firewall matcher that allows capturing traffic based on the present speed of the connection |
| connection-state (established | invalid | new | related | untracked; Default: ) | Interprets the connection tracking analytics data for a particular packet:established - a packet that belongs to an existing connectioninvalid - a packet that does not have a determined state in connection tracking (usually - severe out-of-order packets, packets with wrong sequence/ack number, or in case of a resource over usage on the router), for this reason, an invalid packet will not participate in NAT (as only connection-state=new packets do), and will still contain original source IP address when routed. We strongly suggest dropping all connection-state=invalid packets in the firewall filter forward and input chains- new - the packet has started a new connection, or is otherwise associated with a connection that has not seen packets in both directions.
related - a packet that is related to, but not parts of an existing connection, such as ICMP errors or a packet that begins an FTP data connectionuntracked - packet which was set to bypass connection tracking in firewall RAW tables.
|
| connection-type (ftp | h323 | irc | pptp | quake3 | sip | tftp; Default: ) | Matches packets from related connections based on information from their connection tracking helpers. A relevant connection helper must be enabled under /ip firewall service-port |
| content (string; Default: ) | Match packets that contain specified text |
| dscp (integer: 0..63; Default: ) | Matches DSCP IP header field. |
| dst-address (IP/netmask | IP range; Default: ) | Matches packets whose destination is equal to a specified IP or falls into a specified IP range. |
| dst-address-list (name; Default: ) | Matches the destination address of a packet against a user-defined address list |
| dst-address-type (unicast | local | broadcast | multicast; Default: ) | Matches destination address type:unicast - IP address used for point-to-point transmissionlocal - if dst-address is assigned to one of the router's interfacesbroadcast - packet is sent to all devices in a subnetmulticast - packet is forwarded to a defined group of devices
|
| dst-limit (integer[/time],integer,dst-address | dst-port | src-address[/time]; Default: ) | Matches packets until a given PPS limit is exceeded. As opposed to the limit matcher, every destination IP address/destination port has its own limit. Parameters are written in the following format: count[/time],burst,mode[/expire].- count - maximum average packet rate measured in packets per
time interval - time - specifies the time interval in which the packet rate is measured (optional)
- burst - number of packets that are not counted by packet rate
- mode - the classifier for packet rate limiting
- expire - specifies interval after which recorded IP address /port will be deleted (optional)
|
| dst-port (integer[-integer]: 0..65535; Default: ) | List of destination port numbers or port number ranges in format Range[,Port], for example, dst-port=123-345,456-678 |
Matches packets received from HotSpot clients against various HotSpot matchers.auth - matches authenticated HotSpot client packetsfrom-client - matches packets that are coming from the HotSpot clienthttp - matches HTTP requests sent to the HotSpot serverlocal-dst - matches packets that are destined to the HotSpot serverto-client - matches packets that are sent to the HotSpot client |
| icmp-options (integer:integer; Default: ) | Matches ICMP type: code fields |
| in-bridge-port (name; Default: ) | Actual |
interface the packet has entered the router if the incoming is a bridge| in-interface (name; Default: ) | Interface the packet has entered the router |
| ingress-priority (integer: 0..63; Default: ) | Matches ingress the priority of the packet. Priority may be derived from VLAN, WMM or MPLS EXP bit. Read more>> |
| ipsec-policy (in | out, ipsec | none; Default: ) | Matches the policy used by IpSec. Value is written in the following format: direction, policy. The direction is Used to select whether to match the policy used for decapsulation or the policy that will be used for encapsulation.- in - valid in the PREROUTING, INPUT, and FORWARD chains
- out - valid in the POSTROUTING, OUTPUT, and FORWARD chains
- ipsec - matches if the packet is subject to IpSec processing;
- none - matches packet that is not subject to IpSec processing (for example, IpSec transport packet).
For example, if a router receives an IPsec encapsulated Gre packet, then rule ipsec-policy=in,ipsec will match Gre packet, but the rule ipsec-policy=in,none will match the ESP packet. |
ipv4-options (any | loose-source-routing | no-record-route | no-router-alert | no-source-routing | no-timestamp | none | record-route | router-alert | strict-source-routing | timestamp; Default: ) | | the packet has entered the router if the incoming interface is a bridge |
| in-bridge-port-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as in-bridge-port |
| in-interface (name; Default: ) | Interface the packet has entered the router |
| in-interface-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as in-interface |
| ingress-priority (integer: 0..63; Default: ) | Matches ingress the priority of the packet. Priority may be derived from VLAN, WMM or MPLS EXP bit. |
| ipsec-policy (in | out, ipsec | none; Default: ) | Matches the policy used by IPSec. Value is written in the following format: direction, policy. The direction is Used to select whether to match the policy used for decapsulation or the policy that will be used for encapsulation.in - valid in the PREROUTING, INPUT, and FORWARD chainsout - valid in the POSTROUTING, OUTPUT, and FORWARD chains
ipsec - matches if the packet is subject to IPsec processing;none - matches packet that is not subject to IPsec processing (for example, IPSec transport packet).
For example, if a router receives an IPsec encapsulated Gre packet, then the rule ipsec-policy=in,ipsec will match the Gre packet, but the rule ipsec-policy=in,none will match the ESP packet. |
Matches IPv4 header options.any - match packet with at least one of the ipv4 optionsloose-source-routing - match packets with a loose source routing option. This option is used to route the internet datagram based on information supplied by the sourceno-record-route - match packets with no record route option. This option is used to route the internet datagram based on information supplied by the sourceno-router-alert - match packets with no router alter optionno-source-routing - match packets with no source routing optionno-timestamp - match packets with no timestamp optionrecord-route - match packets with record route optionrouter-alert - match packets with router alter optionstrict-source-routing - match packets with strict source routing optiontimestamp - match packets with a timestamp |
| jump-target (name; Default: ) | Name of the target chain to jump to. Applicable only if action=jump |
| layer7-protocol (name; Default: ) | Layer7 filter name defined in layer7 protocol menu. |
| limit (integer,time,integer; Default: ) | Matches packets until a given PPS limit is exceeded. Parameters are written in the following format: count[/time],burst.- count - maximum average packet rate measured in packets per
time interval - time - specifies the time interval in which the packet rate is measured (optional, 1s will be used if not specified)
- burst
|
- number of packets that are not counted by packet rate- - number of packets that are not counted by packet rate
|
| log (yes | no; Default: no) | Add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port, and length of the packet. |
| log-prefix (string; Default: ) | Adds specified text at the beginning of every log message. Applicable if action=log or log |
=yes configured. |
| out-bridge-port (name |
nth (integer,integerMatches every nth packet: nth=2,1 rule will match every first packet of 2, hence, 50% of all the traffic that is matched by the rule | | Actual interface the packet is leaving the router if the outgoing interface is a bridge |
| out-bridge-port-list (name; Default: ) | Set of interfaces defined in interface list. Works the same as out-bridge-port |
| out-interface ( |
nameActual interface | Interface the packet is leaving the router |
if the outgoing interface is a bridge |
| out-interface-list (name; Default: ) |
Interface the packet is leaving the router| Set of interfaces defined in interface list. Works the same as out-interface |
| packet-mark (no-mark | string; Default: ) | Matches packets marked via mangle facility with particular packet mark. If no-mark is set, the rule will match any unmarked packet |
| packet-size (integer[-integer]:0..65535; Default: ) | Matches packets of specified size or size range in bytes |
| per-connection-classifier (ValuesToHash:Denominator/Remainder; Default: ) | PCC matcher allows dividing traffic into equal streams with the ability to keep packets with a specific set of options in one particular stream |
| port (integer[-integer]: 0..65535; Default: ) | Matches if any (source or destination) port matches the specified list of ports or port ranges. Applicable only if protocol is TCP or UDP |
| protocol (name or protocol ID; Default: tcp) | Matches particular IP protocol specified by protocol name or |
numberpsd (integer,time,integer,integer; Default: ) | Attempts to detect TCP and UDP scans. Parameters are in the following format WeightThreshold, DelayThreshold, LowPortWeight, HighPortWeight| number |
| priority (integer: 0..63; Default:) | Matches the packet's priority after a new priority has been set. Priority may be derived from VLAN, WMM, DSCP, MPLS EXP bit, or from the priority that has been set using the set-priority action. |
WeightThreshold - total weight of the latest TCP/UDP packets with different destination ports coming from the same host to be treated as port scan sequenceDelayThreshold - delay for the packets with different destination ports coming from the same host to be treated as possible port scan subsequenceLowPortWeight - the weight of the packets with privileged (<1024) destination portHighPortWeight - the weight of the packet with non-privileged destination port |
| random (integer: 1..99; Default: ) | Matches packets randomly with a given probability |
| routing-mark (string; Default: ) | Matches packets marked by mangle facility with particular routing mark |
same-not-by-dst (yes | no; Default: )Specifies whether to take into account or not destination IP address when selecting a new source IP address. Applicable if action=same | | src-address (Ip/Netmaks, Ip range; Default: ) | Matches packets |
which | whose source is equal to a specified IP or falls into a specified IP range. |
| src-address-list (name; Default: ) | Matches the source address of a packet against a user-defined address list |
| src-address-type (unicast | local | broadcast | multicast; Default: ) | Matches source address type: unicast - IP address used for point-to-point transmissionlocal - if an address is assigned to one of the router's interfacesbroadcast - packet is sent to all devices in a subnet
|
multicast multicast - packet is forwarded to a defined group of devices
|
| src-port (integer[-integer]: 0..65535; Default: ) | List of source ports and ranges of source ports. Applicable only if a protocol is |
TCP or UDP.| TCP or UDP. |
| tcp-flags (ack | cwr | ece | fin | psh | rst | syn | urg; Default: ) | Matches specified TCP flagsack - acknowledging datacwr - congestion window reducedece - ECN-echo flag (explicit congestion notification)fin - close connectionpsh - push functionrst - drop connectionsyn - new connectionurg - urgent data
|
| src-mac-address (MAC address; Default: ) | Matches the source MAC address of the packet |
| tcp-mss (integer[-integer]: 0..65535; Default: ) | Matches the TCP MSS value of an IP packet |
| time (time-time,sat | fri | thu | wed | tue | mon | sun; Default: ) | Allows to create a filter based on the packets' arrival time and date or, for locally generated packets, departure time and date |
| to-addresses (IP address[-IP address]; Default: 0.0.0.0) | Replace the original address with the specified one. Applicable if action is dst-nat, netmap, same, src-nat |
| to-ports (integer[-integer]: 0..65535; Default: ) | Replace the original port with the specified one. Applicable if action is dst-nat, redirect, masquerade, netmap, same, src-nat |
| ttl (integer: 0..255; Default: ) | Matches packets TTL value |
Stats
| Property | Description |
|---|
| bytes (integer) | The total amount of bytes matched by the rule |
| packets (integer) | The total amount of packets matched by the rule |
To show additional read-only properties:
| Code Block |
|---|
|
[admin@MikroTik] > ip firewall nat print stats all
Flags: X - disabled, I - invalid, D - dynamic
# CHAIN ACTION BYTES PACKETS
0 srcnat masquerade 265 659 987ipv6/firewall/nat/print stats |