...
- certificate is not yet valid - notBefore certificate date is after the current time;
- certificate has expired - certificate expiry date is before the current time;
- cinvalid certificate purpose - the supplied certificate cannot be used for the specified purpose;
- cself signed certificate in a chain - the certificate chain could be built up using the untrusted certificates but the root could not be found locally;
- cunable to get issuer certificate locally - CA certificate is not imported locally;
- cserver's IP address does not match certificate - server address verification is enabled, but the address provided in certificate does not match the server's address;
Configuration example
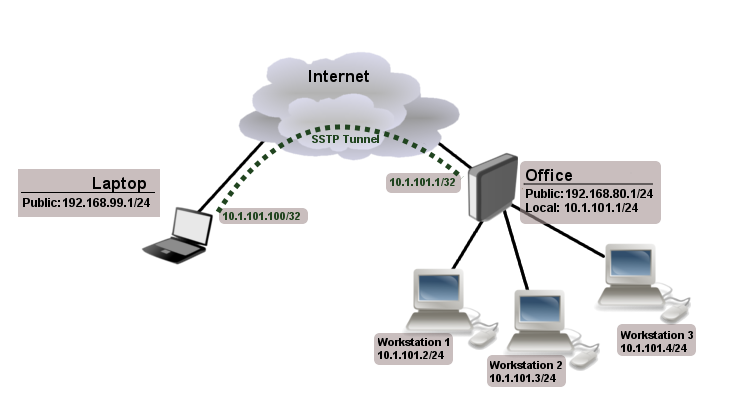
The following example shows how to connect a computer to a remote office network over secure SSTP encrypted tunnel giving that computer an IP address from the same network as the remote office has (without the need for bridging over EoIP tunnels)
Consider the following setup:
Office router is connected to the internet through ether1. Workstations are connected to ether2. A laptop is connected to the internet and can reach Office router's public IP (in our example it is 192.168.80.1).
| Note |
|---|
Before you begin to configure SSTP you need to create a server certificate and import it into the router. |
Now it is time to create a user:
/ppp secretaddname=Laptopservice=sstppassword=123local-address=10.1.101.1remote-address=10.1.101.100
/ppp secret print detail
Flags: X - disabled 0 name="Laptop" service=sstp caller-id="" password="123" profile=default local-address=10.1.101.1 remote-address=10.1.101.100 routes==""
Notice that SSTP local address is the same as the router's address on the local interface and the remote address is from the same range as the local network (10.1.101.0/24).
Next step is to enable SSTP server and SSTP client on the laptop:
/interface sstp-server serversetcertificate=server/interface sstp-server serversetenabled=yes/interface sstp-server serversetauthentication=mschap2
/interface sstp-server server print enabled: yes port: 443 max-mtu: 1500 max-mru: 1500 mrru: disabled keepalive-timeout: 60 default-profile: default certificate: server verify-client-certificate: no authentication: mschap2
Notice that authentication is set to MS-CHAP. These are the only authentication options that are valid to establish a secure tunnel.
SSTP client from the laptop should connect to routers public IP which in our example is 192.168.80.1.
Please, consult the respective manual on how to set up an SSTP client with the software you are using. If you set up SSTP clients on Windows and self-signed certificates are used, then a CA certificate should be added to a trusted root.
To verify if SSTP client is connected
/interface sstp-server print
Flags: X - disabled, D - dynamic, R - running
# NAME USER MTU CLIENT-ADDRESS UPTIME ENCODING
0 DR sstp-... Laptop 1500 10.1.101.18:43886 1h47s
/interface sstp-server monitor 0
status: "connected"
uptime: 1h45s
idle-time: 1h45s
user: "Laptop"
caller-id: "192.168.99.1:43886"
mtu: 1500At this point (when SSTP client is successfully connected) if you try to ping any workstation from a laptop, ping will time out, because the Laptop is unable to get ARP`s from workstations. The solution is to set up proxy-arp on a local interface
/interface ethernet set ether2 arp=proxy-arpAfter proxy-arp is enabled client can successfully reach all workstations in the local network behind the router.