| Table of Contents |
|---|
Introduction
Firewall filters are used to allow or block specific packets forwarded to your local network, originated originating from your router, or destined to the router.
...
Both methods have pros and cons, for example, from a security point of view first method is much more secure, but requires administrator input whenever traffic for a new service needs to be accepted. This strategy provides good control over the traffic and reduces the possibility of a breach because of service misconfiguration.
...
A firewall filter consists of three predefined chains that cannot be deleted:
- input - used to process packets entering the router through one of the interfaces with the destination IP address which is one of the router's addresses. Packets passing through the router are not processed against the rules of the input chain
- forward - used to process packets passing through the router
- output - used to process packets originated originating from the router and leaving it through one of the interfaces. Packets passing through the router are not processed against the rules of the output chain
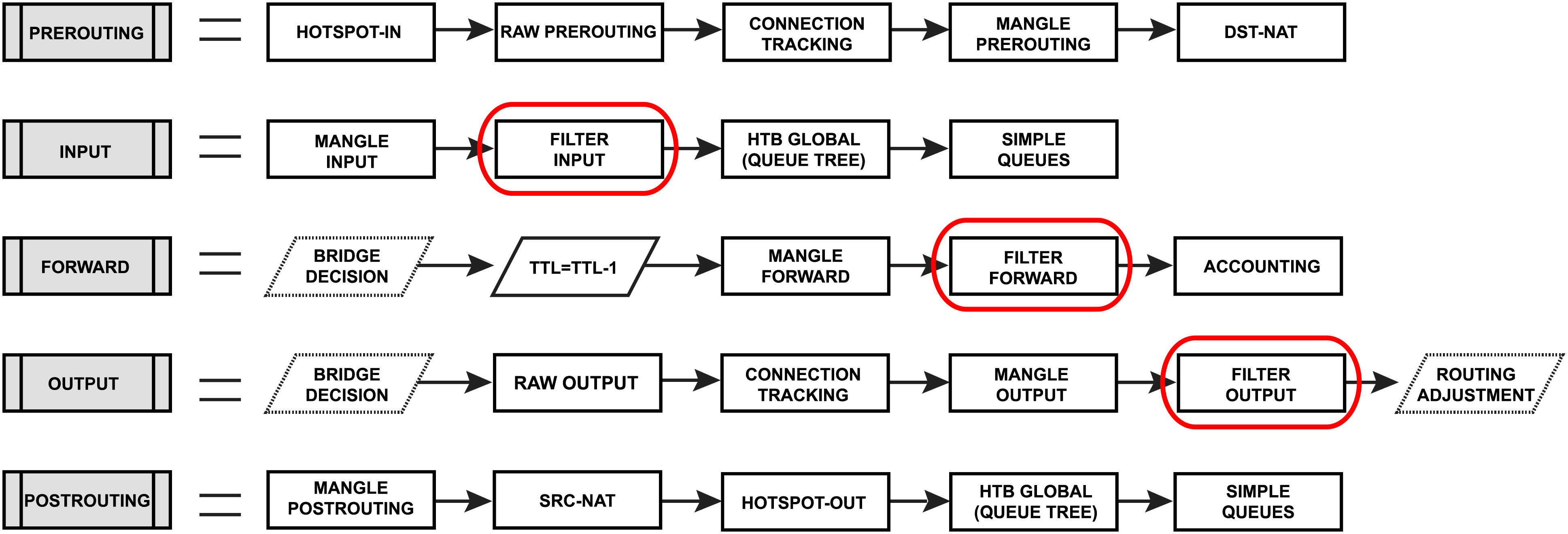
When processing a chain, rules are taken from the chain in the order they are listed there from top to bottom. If a packet matches the criteria of the rule, then the specified action is performed on it, and no more rules are processed in that chain (the exception is the passthrough action). If a packet has not matched any rule within the built-in chain, then it is accepted. More detailed packet processing in RouterOS is described in the Packet Flow in RouterOS diagram.
IPv4
Properties
...
- accept - accept the packet. A packet is not passed to the next firewall rule.
- add-dst-to-address-list - add destination address to address list specified by
address-listparameter - add-src-to-address-list - add source address to address list specified by
address-listparameter - drop - silently drop the packet
- fasttrack-connection - process packets from a connection using FastPath by enabling FastTrack for the connection
- jump - jump to the user-defined chain specified by the value of
jump-targetparameter - log - add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port and length of the packet. After a packet is matched it is passed to the next rule in the list, similar as
passthrough - passthrough - if a packet is matched by the rule, increase counter and go to next rule (useful for statistics)
- reject - drop the packet and send an ICMP reject message; this action allows ICMP reply specification, such as: prohibit or unreachable admin/host/network/port
- return - passes control back to the chain from where the jump took place
- tarpit - captures and holds TCP connections (replies with SYN/ACK to the inbound TCP SYN packet)
...
- Value of none-dynamic (
00:00:00) will leave the address in the address list till reboot - Value of none-static will leave the address in the address list forever and will be included in configuration export/backup
...
- established - a packet that belongs to an existing connection
- invalid - a packet that does not have a determined state in connection tracking (usually - severe out-of-order packets, packets with wrong sequence/ack number, or in case of a resource over usage on the router), for this reason, an invalid packet will not participate in NAT (as only connection-state=new packets do), and will still contain original source IP address when routed. We strongly suggest dropping all connection-state=invalid packets in firewall filter forward and input chains
- new - the packet has started a new connection, or otherwise associated with a connection that has not seen packets in both directions.
- related - a packet that is related to, but not parts of an existing connection, such as ICMP errors or a packet that begins FTP data connection
- an untracked - packet which was set to bypass connection tracking in firewall RAW tables.
...
- unicast - IP address used for point to point transmission
- local - if dst-address is assigned to one of the router's interfaces
- broadcast - packet is sent to all devices in a subnet
- multicast - packet is forwarded to a defined group of devices
...
- rate - packet count per time interval per-flow to match
- time - specifies the time interval in which the packet count rate per flow cannot be exceeded (optional, 1s will be used if not specified)
- burst - initial number of packets per flow to match: this number gets recharged by one every
time/rate, up to this number - mode - this parameter specifies what unique fields define flow (src-address, dst-address, src-and-dst-address, dst-address-and-port, addresses-and-dst-port)
- expire - specifies interval after which flow with no packets will be allowed to be deleted (optional)
...
- auth - matches authenticated HotSpot client packets
- from-client - matches packets that are coming from the HotSpot client
- http - matches HTTP requests sent to the HotSpot server
- local-dst - matches packets that are destined to the HotSpot server
- to-client - matches packets that are sent to the HotSpot client
...
- in - valid in the PREROUTING, INPUT, and FORWARD chains
- out - valid in the POSTROUTING, OUTPUT, and FORWARD chains
- ipsec - matches if the packet is subject to IPsec processing;
- none - matches packet that is not subject to IPsec processing (for example, IPSec transport packet).
For example, if a router receives an IPsec encapsulated Gre packet, then rule ipsec-policy=in,ipsec will match Gre packet, but a rule ipsec-policy=in,none will match the ESP packet.
...
- any - match packet with at least one of the ipv4 options
- loose-source-routing - match packets with a loose source routing option. This option is used to route the internet datagram based on information supplied by the source
- no-record-route - match packets with no record route option. This option is used to route the internet datagram based on information supplied by the source
- no-router-alert - match packets with no router alter option
- no-source-routing - match packets with no source routing option
- no-timestamp - match packets with no timestamp option
- record-route - match packets with record route option
- router-alert - match packets with router alter option
- strict-source-routing - match packets with strict source routing option
- timestamp - match packets with a timestamp
...
- rate - packet or bit count per time interval to match
- time - specifies the time interval in which the packet or bit rate cannot be exceeded (optional, 1s will be used if not specified)
- burst - initial number of packets or bits to match: this number gets recharged every 10ms so burst should be at least 1/100 of a rate per second
- mode - packet or bit mode
...
- WeightThreshold - total weight of the latest TCP/UDP packets with different destination ports coming from the same host to be treated as port scan sequence
- DelayThreshold - delay for the packets with different destination ports coming from the same host to be treated as possible port scan subsequence
- LowPortWeight - the weight of the packets with privileged (<1024) destination port
- HighPortWeight - the weight of the packet with non-privileged destination port
...
Firewall filter configuration is accessible from ip/firewall/filter menu for IPv4 and ipv6/firewall/filter menu for IPv6.
Firewall Example
Lets look at basic firewall example to protect router itself and clients behind the router, for both IPv4 and IPv6 protocols.
IPv4 firewall
Protect the router itself
Rules of thumb followed to set up the firewall:
- work with
newconnections to decrease the load on a router; - accept what you need
dropeverything else,log=yescould be set to log some attackers, but keep in mind that it may add some load to he CPU on heavy attacks.
We always start by accepting already known and accepted connections, so the first rule should be to accept "established" and "related" connections.
| Code Block | ||
|---|---|---|
| ||
/ip firewall filter
add action=accept chain=input comment="default configuration" connection-state=established,related |
Now we can proceed by accepting some new connections, in our example we want to allow access ICMP protocol from any address and everything else only from 192.168.88.2-192.168.88.254 address range. For that we create an address list and two firewall rules.
| Code Block | ||
|---|---|---|
| ||
/ip firewall address-list
add address=192.168.88.2-192.168.88.254 list=allowed_to_router
/ip firewall filter
add action=accept chain=input src-address-list=allowed_to_router
add action=accept chain=input protocol=icmp
|
And lastly we drop everything else:
| Code Block | ||
|---|---|---|
| ||
add action=drop chain=input |
Complete set of just created rules:
| Code Block | ||
|---|---|---|
| ||
/ip firewall filter
add action=accept chain=input comment="default configuration" connection-state=established,related
add action=accept chain=input src-address-list=allowed_to_router
add action=accept chain=input protocol=icmp
add action=drop chain=input
/ip firewall address-list
add address=192.168.88.2-192.168.88.254 list=allowed_to_router |
Protect the LAN devices
Concept in protecting the users is very similar, except that in this case we are blocking unwanted traffic and accepting everythign else.
At first we will create address-list with the name "not_in_internet" which we will use for the firewall filter rules:
| Code Block | ||
|---|---|---|
| ||
/ip firewall address-list
add address=0.0.0.0/8 comment=RFC6890 list=not_in_internet
add address=172.16.0.0/12 comment=RFC6890 list=not_in_internet
add address=192.168.0.0/16 comment=RFC6890 list=not_in_internet
add address=10.0.0.0/8 comment=RFC6890 list=not_in_internet
add address=169.254.0.0/16 comment=RFC6890 list=not_in_internet
add address=127.0.0.0/8 comment=RFC6890 list=not_in_internet
add address=224.0.0.0/4 comment=Multicast list=not_in_internet
add address=198.18.0.0/15 comment=RFC6890 list=not_in_internet
add address=192.0.0.0/24 comment=RFC6890 list=not_in_internet
add address=192.0.2.0/24 comment=RFC6890 list=not_in_internet
add address=198.51.100.0/24 comment=RFC6890 list=not_in_internet
add address=203.0.113.0/24 comment=RFC6890 list=not_in_internet
add address=100.64.0.0/10 comment=RFC6890 list=not_in_internet
add address=240.0.0.0/4 comment=RFC6890 list=not_in_internet
add address=192.88.99.0/24 comment="6to4 relay Anycast [RFC 3068]" list=not_in_internet |
Brief firewall filter rule explanation:
- packets with connection-state=established,related added to FastTrack for faster data throughput, the firewall will work with new connections only;
- drop invalid connection and log them with prefix "invalid";
- drop attempts to reach not public addresses from your local network, apply address-list=not_in_internet before, "bridge" is local network interface, log=yes attempts with prefix "!public_from_LAN";
- drop incoming packets that are not NAT`ed, ether1 is public interface, log attempts with "!NAT" prefix;
- jump to ICMP chain to drop unwanted ICMP messages
- drop incoming packets from the Internet, which are not public IP addresses, ether1 is a public interface, log attempts with prefix "!public";
- drop packets from LAN that does not have LAN IP, 192.168.88.0/24 is local network used subnet;
| Code Block | ||
|---|---|---|
| ||
/ip firewall filter
add action=fasttrack-connection chain=forward comment=FastTrack connection-state=established,related
add action=accept chain=forward comment="Established, Related" connection-state=established,related
add action=drop chain=forward comment="Drop invalid" connection-state=invalid log=yes log-prefix=invalid
add action=drop chain=forward comment="Drop tries to reach not public addresses from LAN" dst-address-list=not_in_internet in-interface=bridge log=yes log-prefix=!public_from_LAN out-interface=!bridge
add action=drop chain=forward comment="Drop incoming packets that are not NAT`ted" connection-nat-state=!dstnat connection-state=new in-interface=ether1 log=yes log-prefix=!NAT
add action=jump chain=forward protocol=icmp jump-target=icmp comment="jump to ICMP filters"
add action=drop chain=forward comment="Drop incoming from internet which is not public IP" in-interface=ether1 log=yes log-prefix=!public src-address-list=not_in_internet
add action=drop chain=forward comment="Drop packets from LAN that do not have LAN IP" in-interface=bridge log=yes log-prefix=LAN_!LAN src-address=!192.168.88.0/24 |
Allow only needed ICMP codes in "icmp" chain:
| Code Block | ||
|---|---|---|
| ||
/ip firewall filter
add chain=icmp protocol=icmp icmp-options=0:0 action=accept \
comment="echo reply"
add chain=icmp protocol=icmp icmp-options=3:0 action=accept \
comment="net unreachable"
add chain=icmp protocol=icmp icmp-options=3:1 action=accept \
comment="host unreachable"
add chain=icmp protocol=icmp icmp-options=3:4 action=accept \
comment="host unreachable fragmentation required"
add chain=icmp protocol=icmp icmp-options=8:0 action=accept \
comment="allow echo request"
add chain=icmp protocol=icmp icmp-options=11:0 action=accept \
comment="allow time exceed"
add chain=icmp protocol=icmp icmp-options=12:0 action=accept \
comment="allow parameter bad"
add chain=icmp action=drop comment="deny all other types" |
IPv6 firewall
Protect the router itself
Very similar to IPv4 setup, except that we have to deal with more protocols required for IPv6 to function properly.
At first we create an address-list from which you allow access to the device:
| Code Block | ||
|---|---|---|
| ||
/ipv6 firewall address-list add address=fd12:672e:6f65:8899::/64 list=allowed |
Brief IPv6 firewall filter rule explanation:
- work with new packets, accept established/related packets;
- drop link-local addresses from Internet(public) interface/interface-list;
- accept access to a router from link-local addresses, accept multicast addresses for management purposes, accept your source address-list for router access;
- drop anything else;
| Code Block | ||
|---|---|---|
| ||
/ipv6 firewall filter
add action=accept chain=input comment="allow established and related" connection-state=established,related
add chain=input action=accept protocol=icmpv6 comment="accept ICMPv6"
add chain=input action=accept protocol=udp port=33434-33534 comment="defconf: accept UDP traceroute"
add chain=input action=accept protocol=udp dst-port=546 src-address=fe80::/10 comment="accept DHCPv6-Client prefix delegation."
add action=drop chain=input in-interface=in_interface_name log=yes log-prefix=dropLL_from_public src-address=fe80::/10
add action=accept chain=input comment="allow allowed addresses" src-address-list=allowed
add action=drop chain=input
/ipv6 firewall address-list
add address=fe80::/16 list=allowed
add address=xxxx::/48 list=allowed
add address=ff02::/16 comment=multicast list=allowed |
| Note |
|---|
In certain setups where the DHCPv6 relay is used, the src address of the packets may not be from the link-local range. In that case, the src-address parameter of rule #4 must be removed or adjusted to accept the relay address. |
Protect the LAN devices
This step is more important than it is for IPv4. In IPv4 setups clients mostly have addresses from local address range and are NATed to public IP, that way they are not directly reachable from the public networks.
IPv6 is a different story. In most common setups, enabled IPv6 makes your clients available from the public networks, so proper firewall filter rules to protect your customers are mandatory.
In brief we will very basic LAN protection should:
- accept established/related and work with new packets;
- drop invalid packets;
- accept ICMPv6 packets;
- accept new connections originated only from your clients to the public network;
- drop everything else.
| Code Block | ||
|---|---|---|
| ||
/ipv6 firewall filter
add action=accept chain=forward comment=established,related connection-state=established,related
add action=drop chain=forward comment=invalid connection-state=invalid log=yes log-prefix=ipv6,invalid
add action=accept chain=forward comment=icmpv6 in-interface=!in_interface_name protocol=icmpv6
add action=accept chain=forward comment="local network" in-interface=!in_interface_name src-address-list=allowed
add action=drop chain=forward log-prefix=IPV6 |
Matchers
All matcher properties are common and listed here.
Actions
Tables below shows list of filter specific actions and associated properties. Other actions are listed here.
| Property | Description |
|---|---|
| action (action name; Default: accept) |
|
| reject-with (icmp-admin-prohibited | icmp-net-prohibited | icmp-protocol-unreachable | icmp-host-prohibited | icmp-network-unreachable | tcp-reset | icmp-host-unreachable | icmp-port-unreachable; Default: icmp-network-unreachable) | Specifies ICMP error to be sent back if the packet is rejected. Applicable if |
RAW Filtering
The firewall RAW table allows to selectively bypass or drop packets before connection tracking, that way significantly reducing the load on the CPU. The tool is very useful for DoS/DDoS attack mitigation.
RAW filter configuration is accessible from ip/firewall/raw menu for IPv4 and ipv6/firewall/raw menu for IPv6.
The RAW table does not have matchers that depend on connection tracking ( like connection-state, layer7, etc.).
If a packet is marked to bypass the connection tracking packet de-fragmentation will not occur.
Also RAW firewall can have rules only in two chains:
- prerouting - used to process any packet entering the router
- output - used to process packets originated from the router and leaving it through one of the interfaces. Packets passing through the router are not processed against the rules of the output chain
And has one specific action:
| Property | Description |
|---|---|
| action (action name; Default: accept) |
|
Basic RAW Example
Let's assume that we have OSPF configuration, but due to connection tracking OSPF have adjacency problems. We can use RAW rules to fix this, by not sending OSPF packets to connection tracking.
| Code Block | ||
|---|---|---|
| ||
/ip firewall raw
add chain=prerouting protocol=ospf action=notrack
add chain=output protocol=ospf action=notrack |
Read More
Specifies ICMP error to be sent back if the packet is rejected. Applicable if action=reject
...
mote{ta{tableMatches source address type:
- unicast - IP address used for point to point transmission
- local - if an address is assigned to one of the router's interfaces
- broadcast - packet is sent to all devices in the subnet
- multicast - packet is forwarded to a defined group of devices
...
- ack - acknowledging data
- cwr - congestion window reduced
- ece - ECN-echo flag (explicit congestion notification)
- fin - close connection
- psh - push function
- rst - drop connection
- syn - new connection
- urg - urgent data
...
Stats
To show additional read-only properties:
| Code Block | ||
|---|---|---|
| ||
/ip firewall filter print stats |
...
| Code Block | ||
|---|---|---|
| ||
[admin@MikroTik] > ip firewall filter print stats
Flags: X - disabled, I - invalid, D - dynamic
# CHAIN ACTION BYTES PACKETS
0 D ;;; special dummy rule to show fasttrack counters
forward passthrough 50 507 925 242 50 048 246
1 ;;; defconf: drop invalid
forward drop 432 270 9 719
2 ;;; defconf: drop invalid
input drop 125 943 2 434
3 input accept 20 090 211 549 20 009 864
4 ;;; defconf: accept ICMP
input accept 634 926 7 648
5 ;;; defconf: drop all not coming from LAN
input drop 4 288 079 83 428
6 ;;; defconf: accept in ipsec policy
forward accept 0 0
7 ;;; defconf: accept out ipsec policy
forward accept 0 0
8 ;;; defconf: fasttrack
forward fasttrack-connection 28 505 528 775 31 504 682
9 ;;; defconf: accept established,related, untracked
forward accept 28 505 528 775 31 504 682
10 ;;; defconf: drop all from WAN not DSTNATed
forward drop 0 0 |
IPv6
| Code Block | ||
|---|---|---|
| ||
/ipv6/firewall/filter |
Properties
...
Property
...
Description
...
- accept - Accept the packet. It is not passed to the next firewall rule.
- add-dst-to-address-list - Add the destination address to address list specified by
address-listparameter - add-src-to-address-list - Add source address to address list specified by
address-listparameter - drop -Silently drop the packet.
- jump - Jump to the user-defined chain specified by the value of
jump-targeta parameter - log - Add a message to the system log containing the following data: in-interface, out-interface, src-mac, protocol, src-ip:port->dst-ip:port and length of the packet. After a packet is matched it is passed to the next rule in the list, similar to
passthrough - passthrough - Ignore this rule and go to the next one (useful for statistics).
- reject - Drop the packet and send an ICMP reject message
- return - Passes control back to the chain from where the jump took place.
...
- Value of none-dynamic (
00:00:00) will leave the address in the address list till reboot - Value of none-static will leave the address in the address list forever and will be included in configuration export/backup
...
- established - a packet that belongs to an existing connection
- invalid - a packet that does not have a determined state in connection tracking (usually - severe out-of-order packets, packets with wrong sequence/ack number, or in case of a resource over usage on the router), for this reason, an invalid packet will not participate in NAT (as only connection-state=new packets do), and will still contain original source IP address when routed. We strongly suggest dropping all connection-state=invalid packets in firewall filter forward and input chains
- new - the packet has started a new connection, or is otherwise associated with a connection that has not seen packets in both directions.
- related - a packet that is related to, but not parts of an existing connection, such as ICMP errors or a packet that begins FTP data connection
- an untracked - packet which was set to bypass connection tracking in firewall RAW tables.
...
- unicast - IP address used for point-to-point transmission
- local - if dst-address is assigned to one of the router's interfaces
- broadcast - packet is sent to all devices in a subnet
- multicast - packet is forwarded to a defined group of devices
...
- rate - packet count per time interval per-flow to match
- time - specifies the time interval in which the packet count rate per flow cannot be exceeded (optional, 1s will be used if not specified)
- burst - initial number of packets per flow to match: this number gets recharged by one every
time/rate, up to this number - mode - this parameter specifies what unique fields define flow (src-address, dst-address, src-and-dst-address, dst-address-and-port, addresses-and-dst-port)
- expire - specifies interval after which flow with no packets will be allowed to be deleted (optional)
...
- in - valid in the PREROUTING, INPUT, and FORWARD chains
- out - valid in the POSTROUTING, OUTPUT, and FORWARD chains
- ipsec - matches if the packet is subject to IPsec processing;
- none - matches packet that is not subject to IPsec processing (for example, IPSec transport packet).
For example, if a router receives an IPsec encapsulated Gre packet, then rule ipsec-policy=in,ipsec will match Gre packet, but a rule ipsec-policy=in,none will match the ESP packet.
...
- rate - packet or bit count per time interval to match
- time - specifies the time interval in which the packet or bit rate cannot be exceeded (optional, 1s will be used if not specified)
- burst - initial number of packets or bits to match: this number gets recharged every 10ms so burst should be at least 1/100 of a rate per second
- mode - packet or bit mode
...
Specifies ICMP error to be sent back if the packet is rejected. Applicable if action=reject
- icmp-address-unreachable: sends ICMP address unreachable message
- icmp-admin-prohibited: sends ICMP address prohibited message
- icmp-no-route: sends ICMP address no-route message
- icmp-not-neighbour: sends ICMP address not-member message
- icmp-port-unreachable: sends ICMP port unreachable message
- tcp-reset: sends ICMP resetting a TCP connection
...
Matches source address type:
- unicast - IP address used for point-to-point transmission
- local - if an address is assigned to one of the router's interfaces
- broadcast - packet is sent to all devices in the subnet
- multicast - packet is forwarded to a defined group of devices
...
- ack - acknowledging data
- cwr - congestion window reduced
- ece - ECN-echo flag (explicit congestion notification)
- fin - close connection
- psh - push function
- rst - drop connection
- syn - new connection
- urg - urgent data
...
Stats
| Code Block | ||
|---|---|---|
| ||
/ipv6/firewall/filter/print/stats |
To show additional read-only properties:
...
Property
...
Description
...
Example
...