...
A packet sniffer is a tool that can capture and analyze packets that are going to, leaving or going through the router. Packet sniffing is very useful when you diagnose networks or protect against security attacks over networks.
| Note |
|---|
Unicast traffic between Wireless clients with client-to-client forwarding enabled will not be visible to the sniffer tool. Packets that are processed with hardware offloading enabled bridge will also not be visible (flooded packets like unknown unicast, broadcast, and multicast traffic might be visible). |
Packet Sniffer configuration
...
In the following example, we will configure the sniffer to match packets going through the ether1 interface:
...
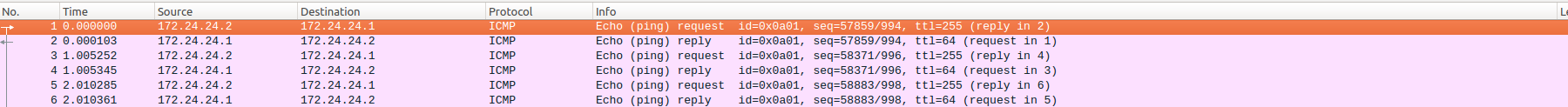
You can download captured packets from a file section. Then you can use a packet analyzer such as Wireshark to analyze a file:
Sub-menu: /tool sniffer
| Property | Description |
|---|---|
| file-limit (integer 10..4294967295[KiB]; Default: 1000KiB) | File size limit. Sniffer will stop when a limit is reached. |
| file-name (string; Default: ) | Name of the file where sniffed packets will be saved. |
| filter-ip-address (ip/mask[,ip/mask] (max 16 items); Default: ) | Up to 16 ip addresses used as a filter |
| filter-mac-address (mac/mask[,mac/mask] (max 16 items); Default: ) | Up to 16 MAC addresses and MAC address masks used as a filter |
| filter-port ([!]port[,port] (max 16 items); Default: ) | Up to 16 comma separated entries used as a filter |
| filter-ip-protocol ([!]protocol[,protocol] (max 16 items); Default: ) | Up to 16 comma separated entries used as a filter. IP protocols (instead of protocol names, protocol numbers can be used)
|
| filter-mac-protocol ([!]protocol[,protocol] (max 16 items); Default: ) | Up to 16 comma separated entries used as a filter. Mac protocols (instead of protocol names, protocol number can be used):
|
| filter-stream (yes | no; Default: yes) | Sniffed packets that are devised for the sniffer server are ignored |
| filter-direction (any | rx | tx; Default: ) | Specifies om which direction filtering will be applied. |
| interface (all | name; Default: all) | Interface name on which sniffer will be running. all indicates that the sniffer will sniff packets on all interfaces. |
| memory-limit (integer 10..4294967295[KiB]; Default: 100KiB) | Memory amount used to store sniffed data. |
| memory-scroll (yes | no; Default: yes) | Whether to rewrite older sniffed data when the memory limit is reached. |
| only-headers (yes | no; Default: no) | Save in the memory only packet's headers, not the whole packet. |
| streaming-enabled (yes | no; Default: no) | Defines whether to send sniffed packets to streaming server. |
| streaming-server (IP; Default: 0.0.0.0) | Tazmen Sniffer Protocol (TZSP) stream receiver. |
| Warning |
|---|
The |
Packet Sniffer Quick Mode
...