 Destination NAT
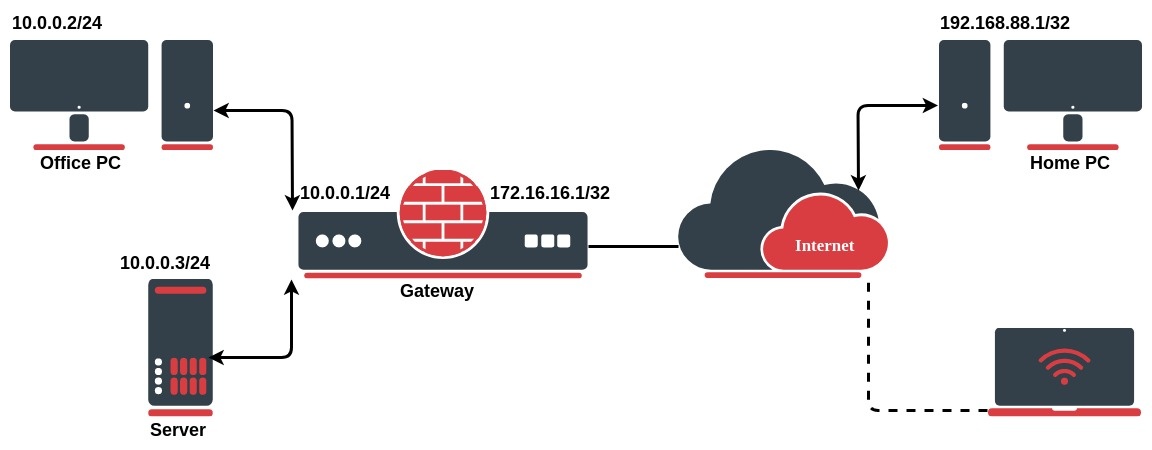
Destination NATNetwork address translation works by modifying network address information in the packets IP header. Let`s take a look at the common setup where a network administrator wants to access an office server from the internet:
We want to allow connections from the internet to the office server whos local IP is 10.0.0.3. In this case, we have to configure a destination address translation rule on the office gateway router:
/ip firewall nat add chain=dstnat action=dst-nat dst-address=172.16.16.1 dst-port=22 to-addresses=10.0.0.3 to-ports=22 protocol=tcp |
The rule above translates: when an incoming connection requests TCP port 22 with destination address 172.16.16.1, use the dst-nat action and depart packets to the device with local IP address 10.0.0.3 and port 22.
To allow access only from the PC at home, we can improve our dst-nat rule with "src-address=192.168.88.1" which is a Home`s PC public IP address. It is also considered to be more secure. |
There might be a necessity allowing the internal server to initiate connections to the outer networks having its source address 10.0.0.3 translated to 172.16.16.1:
/ip firewall nat add chain=srcnat src-address=10.0.0.3 action=src-nat to-addresses=172.16.16.1 |
If you want to hide your local devices behind your public IP address received from ISP, you should configure the source network address translation (masquerading) feature of the MikroTik router.
Let`s assume you want to hide both Office PC and Server behind the public IP 172.16.16.1, the rule will look like the following one:
/ip firewall nat add chain=srcnat src-address=10.0.0.0/24 action=src-nat to-addresses=172.16.16.1 out-interface=WAN |
Now your ISP will see all the requests coming with IP 172.16.16.1 and they will not see your LAN network IP addresses.
Firewall NAT action=masquerade is a unique subversion of action=srcnat, it was designed for specific use in situations when public IP can randomly change, for example, DHCP-server changes it, or PPPoE tunnel after disconnect gets different IP, in short - when public IP is dynamic. Every time interface disconnects and/or its IP address changes, the router will clear all masqueraded connection tracking entries that send a packet out that interface. This improves recovery time after public IP address changes.
Unfortunately, this can lead to some issues when action=masquerade is used in setups with unstable connections/links that get routed over the different links when the primary is down. In such scenario following things can happen:
When action=srcnat is used instead, connection tracking entries remain and connections can simply resume.
/ip firewall nat add chain=srcnat src-address=10.0.0.0/24 action=masquarade out-interface=WAN |