The OpenVPN security model is based on SSL, the industry standard for secure communications via the internet. OpenVPN implements OSI layer 2 or 3 secure network extensions using the SSL/TLS protocol.
OpenVPN has been ported to various platforms, including Linux and Windows, and its configuration is likewise on each of these systems, so it makes it easier to support and maintain. OpenVPN can run over User Datagram Protocol (UDP) or Transmission Control Protocol (TCP) transports, multiplexing created SSL tunnels on a single TCP/UDP port. OpenVPN is one of the few VPN protocols that can make use of a proxy, which might be handy sometimes.
Currently, unsupported OpenVPN features:
OpenVPN username is limited to 27 characters and password to 233 characters.
An interface is created for each tunnel established to the given server. There are two types of interfaces in OVPN server's configuration
Dynamic interfaces appear when a user connects and disappear once the user disconnects, so it is impossible to reference the tunnel created for that use in router configuration (for example, in firewall), so if you need a persistent rule for that user, create a static entry for him/her. Otherwise it is safe to use dynamic configuration.
In both cases PPP users must be configured properly - static entries do not replace PPP configuration. |
| Property | Description |
|---|---|
| auth (sha1 | md5; Default: sha1,md5) | Authentication methods that the server will accept. |
| certificate (name | none; Default: none) | Name of the certificate that the OVPN server will use. |
| cipher (aes128 | aes192 | aes256 | blowfish128; Default: aes128,blowfish128) | Allowed ciphers. |
| default-profile (name; Default: default) | Default profile to use. |
| enabled (yes | no; Default: no) | Defines whether the OVPN server is enabled or not. |
| keepalive-timeout (integer | disabled; Default: 60) | Defines the time period (in seconds) after which the router is starting to send keepalive packets every second. If no traffic and no keepalive responses have come for that period of time (i.e. 2 * keepalive-timeout), not responding client is proclaimed disconnected |
| mac-address (MAC; Default: ) | Automatically generated MAC address of the server. |
| max-mtu (integer; Default: 1500) | Maximum Transmission Unit. Max packet size that the OVPN interface will be able to send without packet fragmentation. |
| mode (ip | ethernet; Default: ip) | Layer3 or layer2 tunnel mode (alternatively tun, tap) |
| netmask (integer; Default: 24) | Subnet mask to be applied to the client. |
| port (integer; Default: 1194) | Port to run the server on. |
| require-client-certificate (yes | no; Default: no) | If set to yes, then the server checks whether the client's certificate belongs to the same certificate chain. |
| redirect-gateway (def1 / disabled / ipv6, Default: disabled) | Specifies what kind of routes the OVPN client must add to the routing table.
|
It is very important that the date on the router is within the range of the installed certificate's date of expiration. To overcome any certificate verification problems, enable NTP date synchronization on both the server and client. |
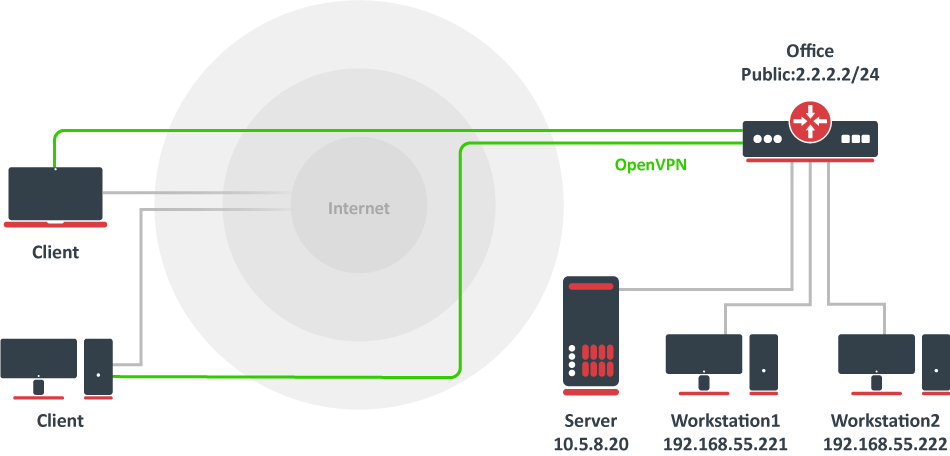
Assume that Office public IP address is 2.2.2.2 and we want two remote OVPN clients to have access to 10.5.8.20 and 192.168.55.0/24 networks behind office gateway.
All certificates can be created on RouterOS server using certificate manager. See example >>.
For simplest setup you need only ovpn server certificate.
First step is to create ip pool from which client addresses will be assigned and some users.
/ip pool add name=ovpn-pool range=192.168.77.2-192.168.77.254 /ppp profile add name=ovpn local-address=192.168.77.1 remote-address=ovpn-pool /ppp secret add name=client1 password=123 profile=ovpn add name=client2 password=234 profile=ovpn |
Assume that server certificate is already created and named "server"
/interface ovpn-server server set enabled=yes certificate=server |
Since RouterOS does not support route-push you need to add manually which networks you want to access over the tunnel.
/interface ovpn-client add name=ovpn-client1 connect-to=2.2.2.2 user=client1 password=123 disabled=no /ip route add dst-address=10.5.8.20 gateway=ovpn-client1 add dst-address=192.168.55.0/24 gateway=ovpn-client1 /ip firewall nat add chain=srcnat action=masquerade out-interface=ovpn-client1 |