Introduction
Internet Protocol Security (IPsec) is a set of protocols defined by the Internet Engineering Task Force (IETF) to secure packet exchange over unprotected IP/IPv6 networks such as the Internet.
IPsec protocol suite can be divided into the following groups:
- Internet Key Exchange (IKE) protocols. Dynamically generates and distributes cryptographic keys for AH and ESP.
- Authentication Header (AH) RFC 4302
- Encapsulating Security Payload (ESP) RFC 4303
Internet Key Exchange Protocol (IKE)
The Internet Key Exchange (IKE) is a protocol that provides authenticated keying material for the Internet Security Association and Key Management Protocol (ISAKMP) framework. There are other key exchange schemes that work with ISAKMP, but IKE is the most widely used one. Together they provide means for authentication of hosts and automatic management of security associations (SA).
Most of the time IKE daemon is doing nothing. There are two possible situations when it is activated:
There is some traffic caught by a policy rule which needs to become encrypted or authenticated, but the policy doesn't have any SAs. The policy notifies IKE daemon about that, and IKE daemon initiates a connection to a remote host. IKE daemon responds to remote connection. In both cases, peers establish a connection and execute 2 phases:
- Phase 1 - The peers agree upon algorithms they will use in the following IKE messages and authenticate. The keying material used to derive keys for all SAs and to protect following ISAKMP exchanges between hosts is generated also. This phase should match the following settings:
- authentication method
- DH group
- encryption algorithm
- exchange mode
- hash algorithm
- NAT-T
- DPD and lifetime (optional)
- Phase 2 - The peers establish one or more SAs that will be used by IPsec to encrypt data. All SAs established by IKE daemon will have lifetime values (either limiting time, after which SA will become invalid, or amount of data that can be encrypted by this SA, or both). This phase should match the following settings:
- IPsec protocol
- mode (tunnel or transport)
- authentication method
- PFS (DH) group
- lifetime
There are two lifetime values - soft and hard. When SA reaches it's soft lifetime treshold, the IKE daemon receives a notice and starts another phase 2 exchange to replace this SA with fresh one. If SA reaches hard lifetime, it is discarded.
Phase 1 is not re-keyed if DPD is disabled when the lifetime expires, only phase 2 is re-keyed. To force phase 1 re-key, enable DPD.
PSK authentication was known to be vulnerable against Offline attacks in "aggressive" mode, however recent discoveries indicate that offline attack is possible also in case of "main" and "ike2" exchange modes. A general recommendation is to avoid using the PSK authentication method.
IKE can optionally provide a Perfect Forward Secrecy (PFS), which is a property of key exchanges, that, in turn, means for IKE that compromising the long term phase 1 key will not allow to easily gain access to all IPsec data that is protected by SAs established through this phase 1. It means an additional keying material is generated for each phase 2.
The generation of keying material is computationally very expensive. Exempli Gratia, the use of the modp8192 group can take several seconds even on a very fast computer. It usually takes place once per phase 1 exchange, which happens only once between any host pair and then is kept for a long time. PFS adds this expensive operation also to each phase 2 exchange.
Diffie-Hellman Groups
Diffie-Hellman (DH) key exchange protocol allows two parties without any initial shared secret to create one securely. The following Modular Exponential (MODP) and Elliptic Curve (EC2N) Diffie-Hellman (also known as "Oakley") Groups are supported:
| Diffie-Hellman Group | Name | Reference |
|---|---|---|
| Group 1 | 768 bit MODP group | RFC 2409 |
| Group 2 | 1024 bits MODP group | RFC 2409 |
| Group 3 | EC2N group on GP(2^155) | RFC 2409 |
| Group 4 | EC2N group on GP(2^185) | RFC 2409 |
| Group 5 | 1536 bits MODP group | RFC 3526 |
| Group 14 | 2048 bits MODP group | RFC 3526 |
| Group 15 | 3072 bits MODP group | RFC 3526 |
| Group 16 | 4096 bits MODP group | RFC 3526 |
| Group 17 | 6144 bits MODP group | RFC 3526 |
| Group 18 | 8192 bits MODP group | RFC 3526 |
| Group 19 | 256 bits random ECP group | RFC 5903 |
| Group 20 | 384 bits random ECP group | RFC 5903 |
| Group 21 | 521 bits random ECP group | RFC 5903 |
More on standards can be found here.
IKE Traffic
To avoid problems with IKE packets hit some SPD rule and require to encrypt it with not yet established SA (that this packet perhaps is trying to establish), locally originated packets with UDP source port 500 are not processed with SPD. The same way packets with UDP destination port 500 that are to be delivered locally are not processed in incoming policy checks.
Setup Procedure
To get IPsec to work with automatic keying using IKE-ISAKMP you will have to configure policy, peer, and proposal (optional) entries.
IPsec is very sensitive to time changes. If both ends of the IPsec tunnel are not synchronizing time equally(for example, different NTP servers not updating time with the same timestamp), tunnels will break and will have to be established again.
EAP Authentication methods
| Outer Auth | Inner Auth |
|---|---|
| EAP-GTC | |
| EAP-MD5 | |
| EAP-MSCHAPv2 | |
| EAP-PEAPv0 | EAP-MSCHAPv2 |
| EAP-SIM | |
| EAP-TLS | |
| EAP-TTLS | PAP |
Authentication Header (AH)
AH is a protocol that provides authentication of either all or part of the contents of a datagram through the addition of a header that is calculated based on the values in the datagram. What parts of the datagram are used for the calculation, and the placement of the header depends on whether tunnel or transport mode is used.
The presence of the AH header allows to verify the integrity of the message but doesn't encrypt it. Thus, AH provides authentication but not privacy. Another protocol (ESP) is considered superior, it provides data privacy and also its own authentication method.
RouterOS supports the following authentication algorithms for AH:
- SHA2 (256, 512)
- SHA1
- MD5
Transport mode
In transport mode, AH header is inserted after the IP header. IP data and header is used to calculate authentication value. IP fields that might change during transit, like TTL and hop count, are set to zero values before authentication.
Tunnel mode
In tunnel mode, the original IP packet is encapsulated within a new IP packet. All of the original IP packets is authenticated.
Encapsulating Security Payload (ESP)
Encapsulating Security Payload (ESP) uses shared key encryption to provide data privacy. ESP also supports its own authentication scheme like that used in AH.
ESP packages its fields in a very different way than AH. Instead of having just a header, it divides its fields into three components:
- ESP Header - Comes before the encrypted data and its placement depends on whether ESP is used in transport mode or tunnel mode.
- ESP Trailer - This section is placed after the encrypted data. It contains padding that is used to align the encrypted data.
- ESP Authentication Data - This field contains an Integrity Check Value (ICV), computed in a manner similar to how the AH protocol works, for when ESP's optional authentication feature is used.
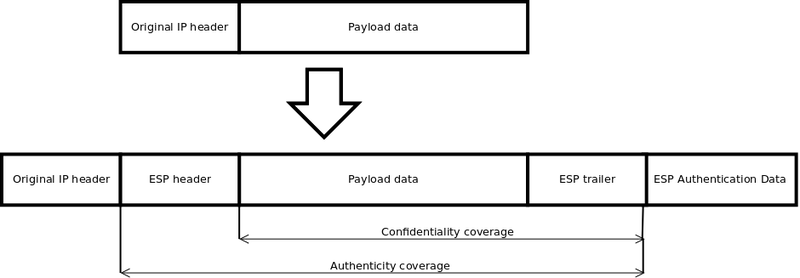
Transport mode
In transport mode, the ESP header is inserted after the original IP header. ESP trailer and authentication value are added to the end of the packet. In this mode only IP payload is encrypted and authenticated, the IP header is not secured.
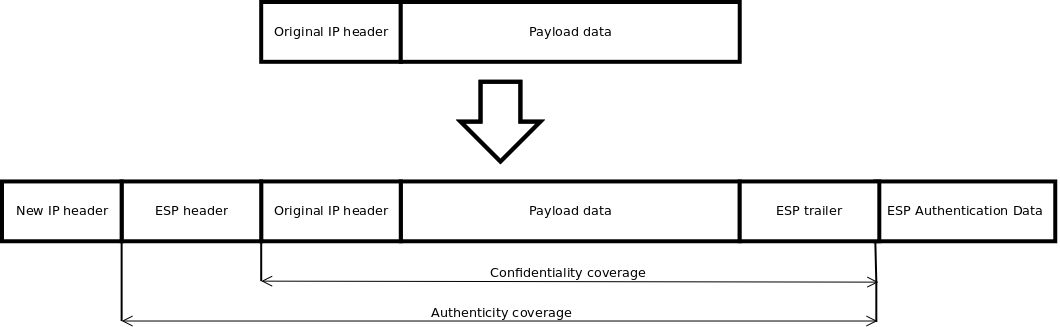
Tunnel mode
In tunnel mode, an original IP packet is encapsulated within a new IP packet thus securing IP payload and IP header.
Encryption algorithms
RouterOS ESP supports various encryption and authentication algorithms.
Authentication:
- MD5
- SHA1
- SHA2 (256-bit, 512-bit)
Encryption:
- AES - 128-bit, 192-bit, and 256-bit key AES-CBC, AES-CTR and AES-GCM algorithms;
- Blowfish - added since v4.5
- Twofish - added since v4.5
- Camellia - 128-bit, 192-bit and 256-bit key Camellia encryption algorithm added since v4.5
- DES - 56-bit DES-CBC encryption algorithm;
- 3DES - 168-bit DES encryption algorithm;
Hardware acceleration
Hardware acceleration allows doing a faster encryption process by using a built-in encryption engine inside the CPU.
| RouterBoard | DES and 3DES | AES-CBC | AES-CTR | AES-GCM | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| MD5 | SHA1 | SHA256 | SHA512 | MD5 | SHA1 | SHA256 | SHA512 | MD5 | SHA1 | SHA256 | SHA512 | MD5 | SHA1 | SHA256 | SHA512 | |
| RBcAPGi-5acD2nD (cAP ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD25G-5HPacQD2HPnD (Audience) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD25GR-5HPacQD2HPnD&R11e-LTE6 (Audience LTE6 kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD52G-5HacD2HnD (hAP ac2) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBDiscG-5acD (DISC Lite5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLDFG-5acD (LDF 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-5acD (LHG 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-5HPacD2HPnD-XL (LHG XL 52 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-5acD-XL (LHG XL 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-60ad (Wireless Wire Dish) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLtAP-2HnD (LtAP) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBLtAP-2HnD&R11e-LTE (LtAP LTE kit) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBLtAP-2HnD&R11e-4G (LtAP 4G kit) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBLtAP-2HnD&R11e-LTE6 (LtAP LTE6 kit) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBM11G **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBM33G **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBSXTsqG-5acD (SXTsq 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPG-60ad (wAP 60G) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPG-60ad-A (wAP 60G AP) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD (wAP R ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD&R11e-LTE (wAP ac LTE kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD&R11e-4G (wAP ac 4G kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD&R11e-LTE6 (wAP ac LTE6 kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RB450Gx4 * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RB750Gr3 (hEX) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RB760iGS (hEX S) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RB850Gx2 ** | no | no | no | no | yes | yes | yes | yes | no | no | no | no | no | no | no | no |
| RB1100AHx2 | yes | yes | yes | no | yes | yes | yes | yes | no | no | no | no | no | no | no | no |
| RB1100AHx4 and RB1100AHx4 Dude Edition | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
| RB1200 *** | no | no | no | no | yes | yes | yes | yes | yes | yes | yes | yes | no | no | no | no |
| RB3011UiAS-RM * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RB4011iGS+RM and RB4011iGS+5HacQ2HnD-IN | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
| Cloud Core Router series | yes | yes | yes | no | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no |
| x86 (AES-NI) *** | no | no | no | no | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
* supported only 128 bit and 256 bit key sizes
** only manufactured since 2016, serial numbers that begin with number 5 and 7
*** AES-CBC and AES-CTR only encryption is accelerated, hashing done in software
**** DES is not supported, only 3DES and AES-CBC
IPsec throughput results of various encryption and hash algorithm combinations are published on MikroTik products page.